BGP Hijacking of Twitter Prefix by RTComm.ru
Earlier today, RTComm.ru started to advertise 104.244.42.0/24, a prefix used by Twitter. RTComm.ru is a sizeable Russian telecom provider. Russian ISPs have started restricting access to Twitter after Russia's invasion of Ukraine led to many Twitter posts critical of Russia's war.
Hijacking a BGP prefix is one way to block access, but it can also be used to intercept traffic to the respective IP addresses. It is not clear if traffic interception is part of the goal here. Twitter typically advertises this same prefix for AS 13414. RTComm.ru uses 8342.
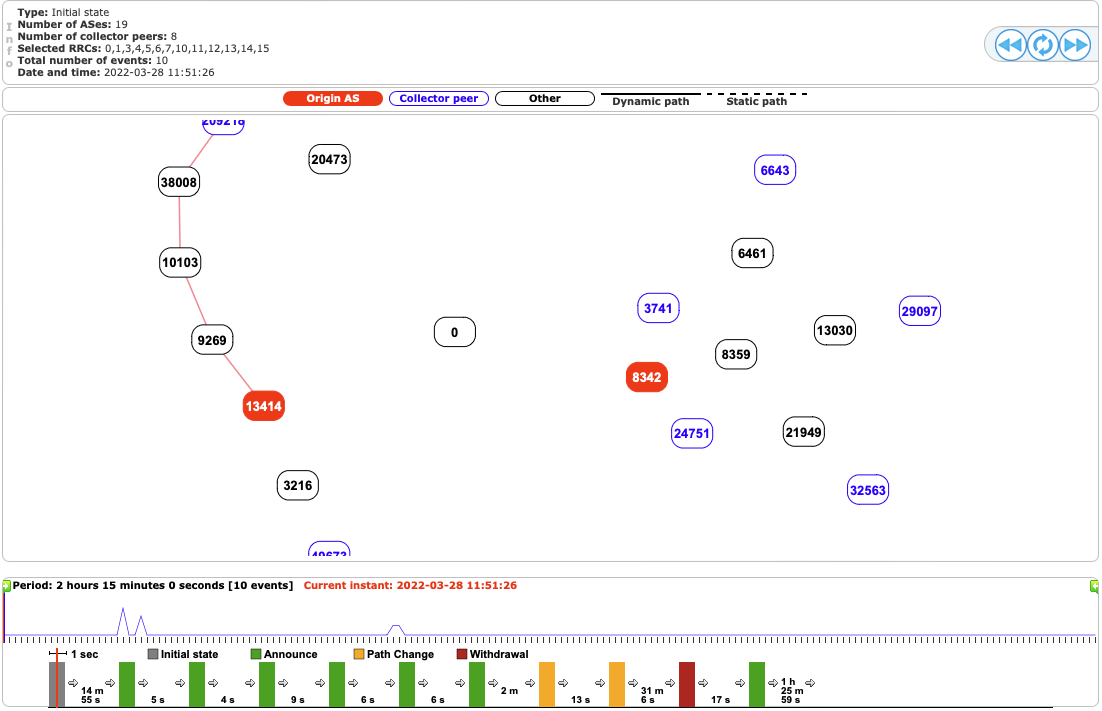
Image from Cisco/BGPStream [1]
BGP announcements can be problematic as they may spread beyond the original target area. In the past, intentional or accidental BGP misconfigurations have led to outages for significant sites. Back in 2008, Pakistan's attempt to block access to YouTube led to YouTube not being available for users worldwide [2]. BGP security has been improved since then, but there is still a possibility that routes "leak." [3]
This is an excellent opportunity to emphasize TLS as an additional layer of protection. "Machine in the middle attacks" (MitM) launched via wrong BGP announcements will lead to certificate warnings if you are visiting a site protected by TLS. TLS not only provides encryption but also authenticates the site you are connecting to. At least as long as you do not trust a certificate authority controlled by the adversary. Certificate pinning, which would detect fake certificates issued by a trusted CA, is not used by current browsers, but some mobile apps may still use it and fail in this more sophisticated (usually state-sponsored) type of MitM attack.
Twitter (a bit ironically here) is probably the simplest way to stay informed about BGP issues. Just follow Cisco's BGPStream account: https://twitter.com/bgpstream
[1] https://bgpstream.com/event/288327
[2] https://www.wired.com/2008/02/pakistans-accid/
[3] https://www.internetsociety.org/deploy360/securing-bgp/
[update: had the AS numbers mixed up in an earlier version]
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|


Comments