More massive malicious spam! This time claiming to be from Almacenes Exito
Last Updated: 2013-04-12 23:17:54 UTC
by Manuel Humberto Santander Pelaez (Version: 1)
------------------------------ BEGIN OF WARNING SECTION ------------------------------
This diary have live malware links, so be careful if you decide to access them.
------------------------------ END OF WARNING SECTION ------------------------------
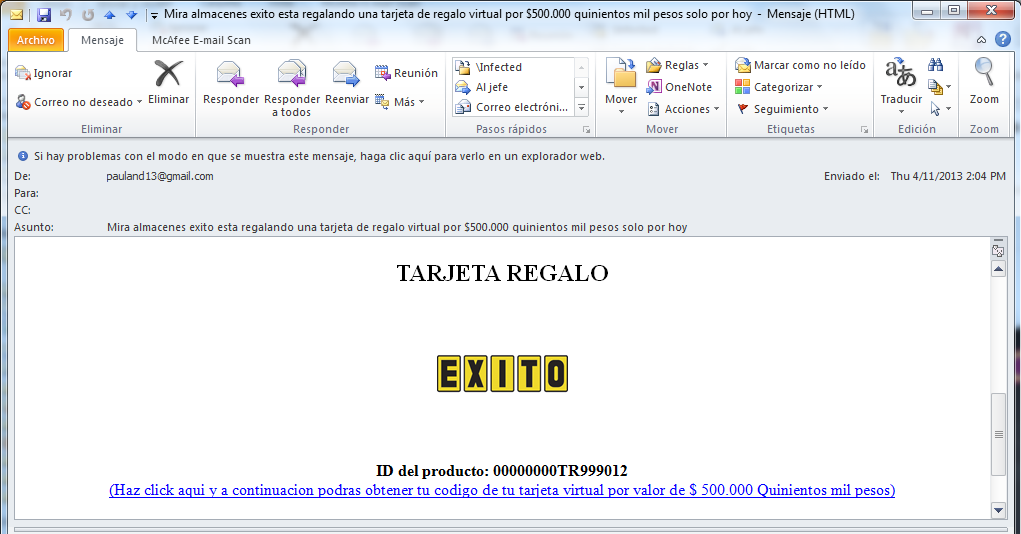
Spammers are busy this week in my Country! Today april 11 2013 I received a spam claiming to be a promotion from the biggest retail company in the country and statng that they are giving for free debit cards for US$274.54.
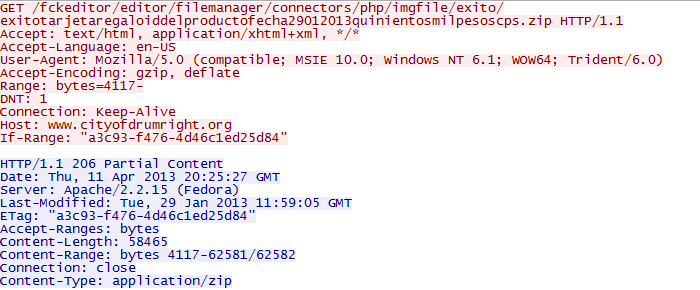
This link points to http://katiepriceuk.com/wp-content/gallery/ecards/www.exito.com.tarjetaderegalo.php. Having a look with wireshark shows the following:
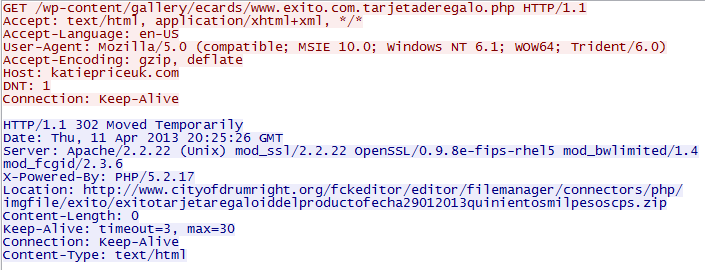
This looks like a vulnerable wordpress site which got modified by a redirect injection. Second one looks like a hacked drupal with the FCKEditor module compromised. Check below:
MD5 for the downloaded zip file is 11da149ca99f2cc9f64c5e4fca76a9f1. The following are the zip content details:
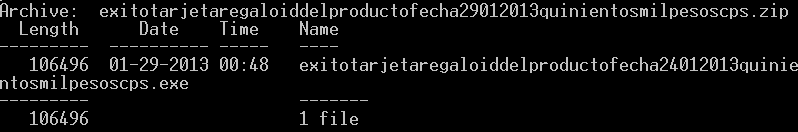
After analyzing this little thing, it turned out to be a koobface variant. Virustotal detection rate is pretty high (36/42), but as I stated in my previous diary, too many people around here does not like to install security controls inside their computers because they do not allow them to use insecure programs or they just think that investing in antimalware / HIPS licenses is not worth it.
If you are in Colombia, please remember that cybercrime is rising and local computer criminals are diseminating specific antimalware targeting banking software from local banks (Bancolombia, Grupo Aval, Corpbanca, ...) and of course every web access you perform to the personal banking sites or payment sites using your banking information. You will do yourself a favor if you invest in basic security controls for your computer like:
- Firewall Software: Windows Firewall is good but lacks advanced functions that really can enhance the protection of your information assets.
- Antimalware: Remember that there are too many malicious software pieces out there, too many of them are not exe files but content delivered through web sites. You need to be protected for malicious javascripts, flash applets, java applets, PDF and so on.
- Host IPS: Most 0-day vulnerabilities can be catched with this protection since it catches buffer overflows and common malicious operations performed by exploits to gain privileges or perform malicious tasks inside your computer.
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter: @manuelsantander
Web:http://manuel.santander.name
e-mail: msantand at isc dot sans dot org

Comments
Vance Baker
Apr 13th 2013
1 decade ago
I'd rather have slightly-slower systems than have to spend _my_ time nuking compromised systems and rebuilding them.
Besides, when's the last time that your "standard" new PC, with dual-cores and two threads per core, ever ran at 100% CPU for enough time for you to notice? It's time to buy a new computer, to replace your Pentium 166 Mhz CPU.
> practicing rudimentary information security precautions
You're waging a "sucker" bet that every computer-user inside your network was paying attention during the tutorial that you gave on the topic (you did give that class, correct?)
ComputerPerformanceEvaluator
Apr 15th 2013
1 decade ago