More Brazil malspam pushing Astaroth (Guildma) in January 2023
Introduction
Tuesday 2023-01-03 and Wednesday 2023-01-04 revealed four Portuguese language emails targetging Brazil. These messages are pushing the same type of Astaroth (Guildma) malware I've seen for the past several months.
2023-01-05 update at 20:24 UTC: list of indicators, malware samples, and packet catpures (pcaps) from two infections related to this diary are now available here.
On an infected Windows host, Astaroth malware is an AutoIt v3 script run by an AutoIt executable. The executable is not inherently malicious on its own. But AutoIt is so closely associated with malware that AutoIt's website has a wiki article noting legitimate AutoIt binaries are often detected as malicious by antivirus vendors (reference).
I've already posted ISC diaries about Astaroth malware in February 2022 and August 2022. Today's diary presents two email templates from recent waves of malspam, and it briefly reviews artifacts from a persistent infection using AutoIt.

Shown above: I should proabably say this is "so hot in Brazil right now."
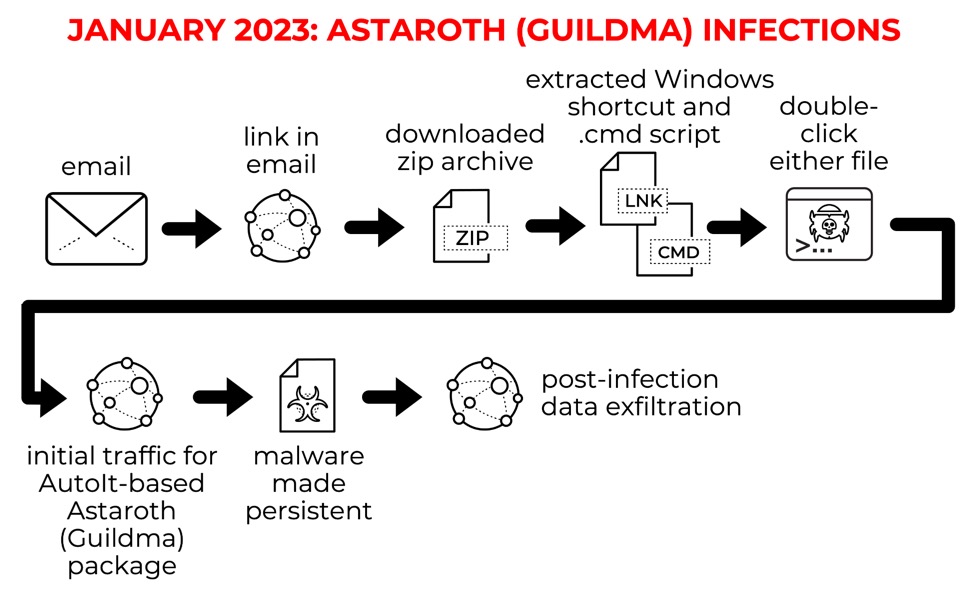
Show above: Flow chart for recent Astaroth (Guildma) infections.
Malspam Examples
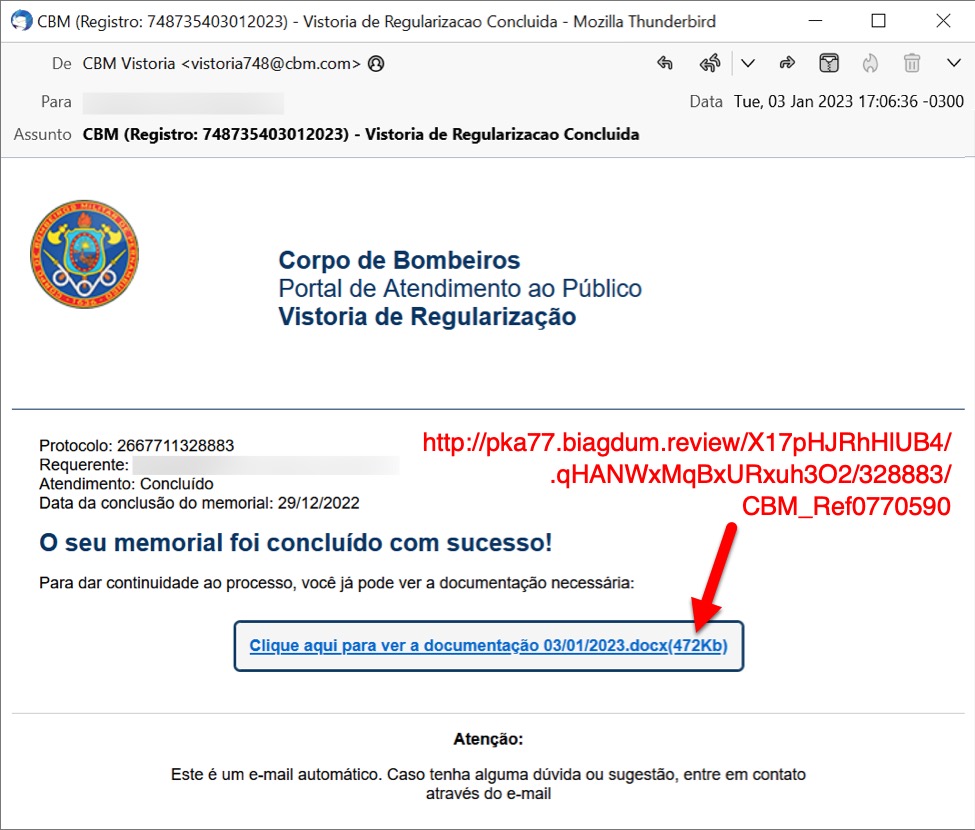
Shown above: Malspam from Tuesday 2023-01-03 pushing Astaroth malware.
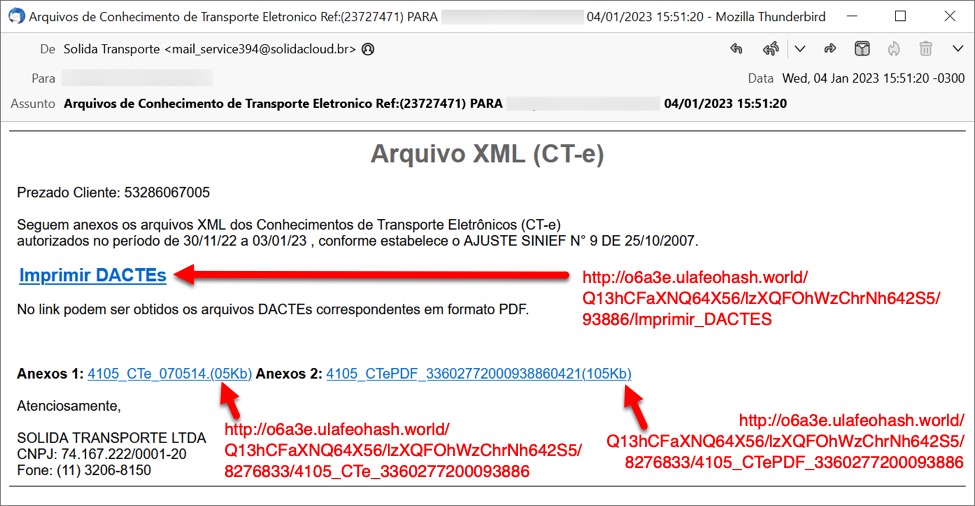
Shown above: Malspam from Wednesday 2023-01-04 pushing Astaroth malware.
Post-Infection Artifacts
Astaroth malware infects a vulnerable Windows host through AutoIt script. The malicious file is an AutoIt v3 compiled script made persistent through a Windows shortcut under the Startup Menu --> Programs --> Startup directory. The malicious script is run by a legitimate AutoIt executable.
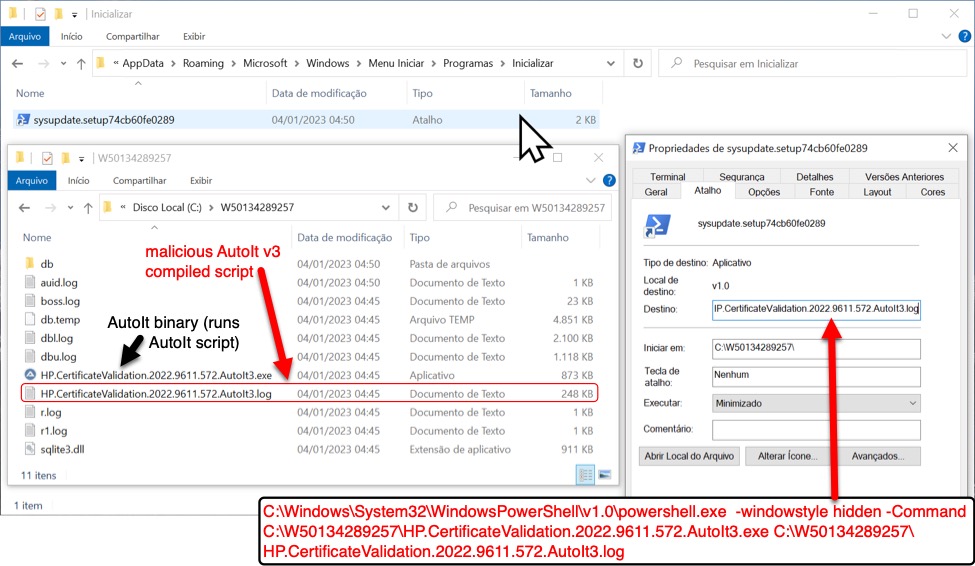
Shown above: Astaroth malware infection made persistent, early on Wendesday 2023-01-04.
Final Words
The following are links from the four emails I've collected so far in 2023.
Links from first email on Tuesday 2023-01-03:
- hxxp://pka77.biagdum[.]review/X17pHJRhHlUB4/.qHANWxMqBxURxuh3O2/328883/CBM_Ref0770590
Links from second email on Tuesday 2023-01-03:
- hxxp://i5ai2h.azuissu[.]directory/E07sWa0JVF3yJz3/ioJFa1sroWslVs3y7I1/357247/CBM_Ref7732548
Links from first email on Wednesday 2023-01-04:
- hxxp://o6a3e.ulafeohash[.]world/Q13hCFaXNQ64X56/lzXQFOhWzChrNh642S5/93886/Imprimir_DACTES
- hxxp://o6a3e.ulafeohash[.]world/Q13hCFaXNQ64X56/lzXQFOhWzChrNh642S5/8276833/4105_CTe_3360277200093886
- hxxp://o6a3e.ulafeohash[.]world/Q13hCFaXNQ64X56/lzXQFOhWzChrNh642S5/8276833/4105_CTePDF_3360277200093886
Links from second email on Wednesday 2023-01-04:
- hxxp://w1oieg.uripawuy[.]town/V19lKMAuK1WH6/r5KPQJkC5HkWAkxu9E1/22356/Imprimir_DACTES
- hxxp://w1oieg.uripawuy[.]town/V19lKMAuK1WH6/r5KPQJkC5HkWAkxu9E1/5134464/4105_CTe_3360277200022356
- hxxp://w1oieg.uripawuy[.]town/V19lKMAuK1WH6/r5KPQJkC5HkWAkxu9E1/5134464/4105_CTePDF_3360277200022356
These URLs are geo-fenced, so they will not provide malware to an English language Windows host from an IP address based in the United States.
A zip archive containing the four emails is available here. Today's diary is a heads-up for this wave of Astaroth/Guildma activity. I will soon post more technical details about the infection traffic on my blog at www.malware-traffic-analysis.net.
2023-01-05 update at 20:24 UTC: list of indicators, malware samples, and packet catpures (pcaps) from two infections related to this diary are now available here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments