sczriptzzbn inject pushes malware for NetSupport RAT
Introduction
A campaign nicknamed "sczriptzzbn inject" can be identified by script using a variable named sczriptzzbn injected into files returned from a compromised website. This injected script causes a fake browser update page to appear in the victim's browser. The fake browser update page presents the malware payload for download. More information on the campaign can be found here. In previous weeks, this campaign pushed SolarMarker malware. I ran across one such example on 2022-09-27. This month, we've started seeing a payload for NetSupport RAT from the sczriptzzbn inject.
Indicators
Path to SolarMarker installer EXE on 2022-09-27:
- hxxp://www.[information redacted].com/meet-robert/ <-- page from compromised website
- hxxp://www.[information redacted].com/wp-includes/js/jquery/jquery.js?ver=.1.12.4-wp <-- sczriptzzbn inject
- hxxps://skambio-porte[.]com/js1 <-- redirect URL to fake update domain
- hxxps://yaritsavodka[.]com/ <-- fake update domain
- hxxps://yaritsavodka[.]com/index-edge.php <-- fake update page for Microsoft Edge
- hxxps://dotimewat[.].com/CLFsecurity.exe <-- SolarMarker presented by fake update page
Note: The fake update page depends on the browser being used. For example:
- hxxps://yaritsavodka[.]com/index-chrome.php
- hxxps://yaritsavodka[.]com/index-edge.php
- hxxps://yaritsavodka[.]com/index-ff.php
EXE installer for SolarMarker malware:
- SHA256 hash: 6371d4c28214de1e599caaede658d752e1fbc691019d8ae34c591a7699911814
- File size: 212,552,264 bytes
- File name: CLFsecurity.exe
Path to EXE installer for NetSupport RAT on 2022-10-20:
- hxxp://www.[information redacted].com/meet-robert/ <-- page from compromised website
- hxxp://www.[information redacted].com/wp-includes/js/jquery/jquery.js?ver=.1.12.4-wp <-- sczriptzzbn inject
- hxxps://pastukhova[.]com/js1 <-- redirect URL to fake update domain
- hxxps://profi-stom[.]com/ <-- fake update domain
- hxxps://yaritsavodka[.]com/index-edge.php <-- fake update page for Microsoft Edge
- hxxps://itraf.org/wp-content/plugins/hello-dolly/Browser_renew.iso <-- Payload for NetSupport RAT presented by fake update page
Downloaded ISO:
- SHA256 hash: 76b3d17196dd9e99eadd46e8bc760ec8809a0c723f66fb687ab8576dd1299e34
- File size: 37,683,200 bytes
- File name: Browser_renew.iso
EXE installer for NetSupport RAT:
- SHA256 hash: 23b14288d49610a8eef61977b7fc49a963f1261fe29b1668b4443a04eaf493cb
- File size: 36,825,879 bytes
- File name: Browser_renew.exe
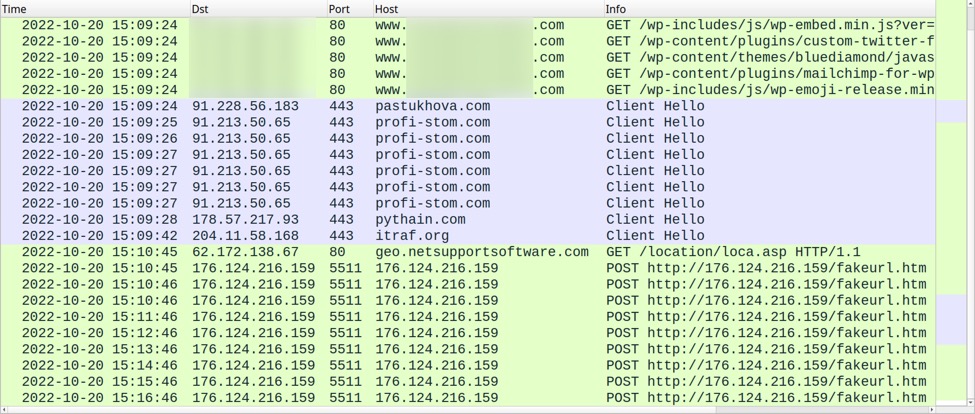
- Shown above: Traffic from the infection filtered in Wireshark.
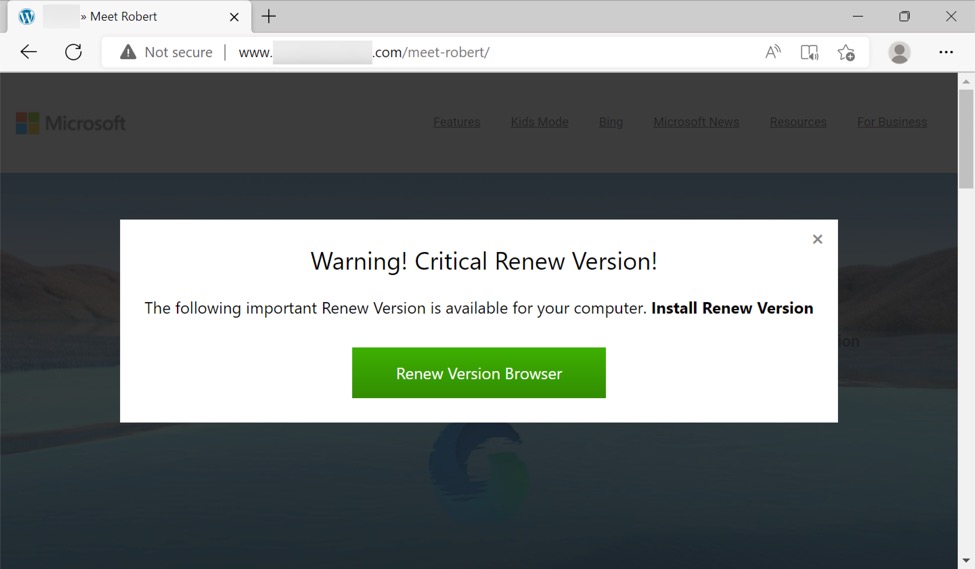
- Shown above: Compromised website with sczriptzzbn inject shows fake update page.
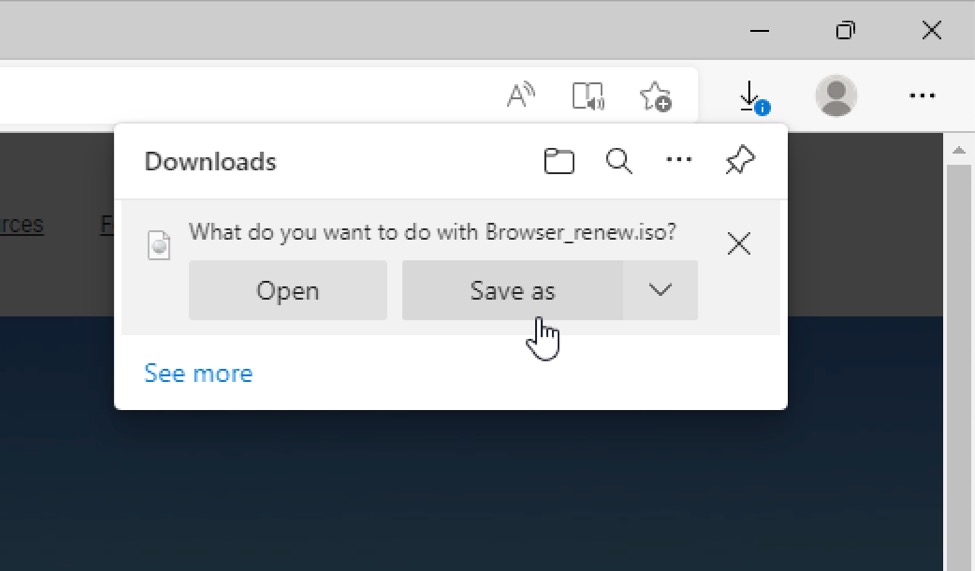
- Shown above: ISO image presented by fake update page.
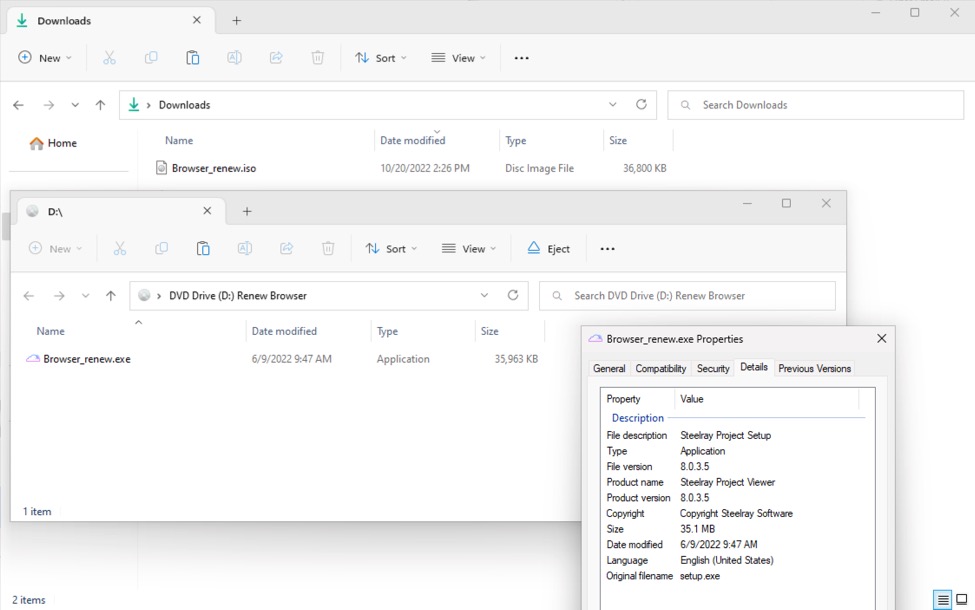
- Shown above EXE extracted from the downloaded ISO image.
The EXE extracted from the ISO image appears to be a stolen and modified installer for the Steelray Project Viewer. When run, this EXE installs Steelray Project Viewer files and NetSupport RAT files.
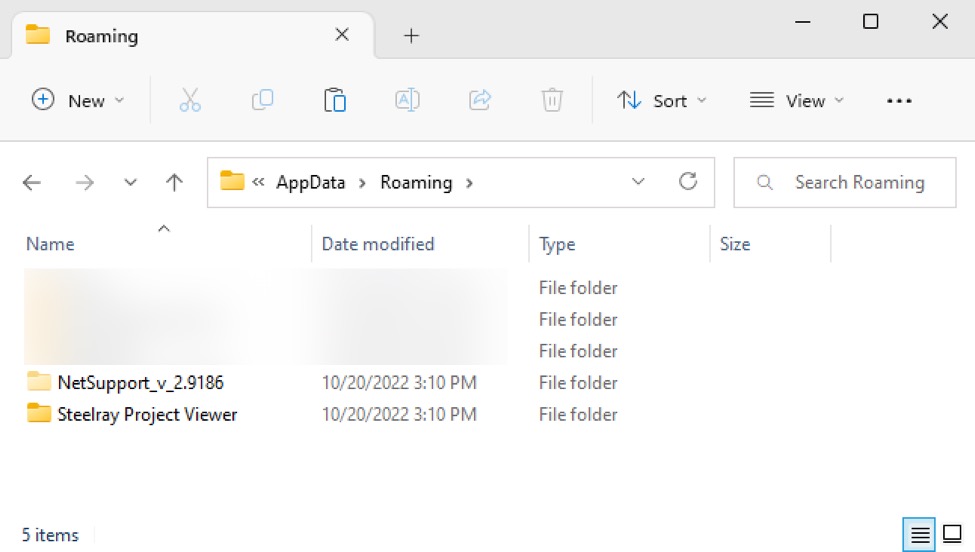
- Shown above: Two directories created by the EXE installer, one for Steelray Project Viewer files, and one for NetSupport Manager RAT.
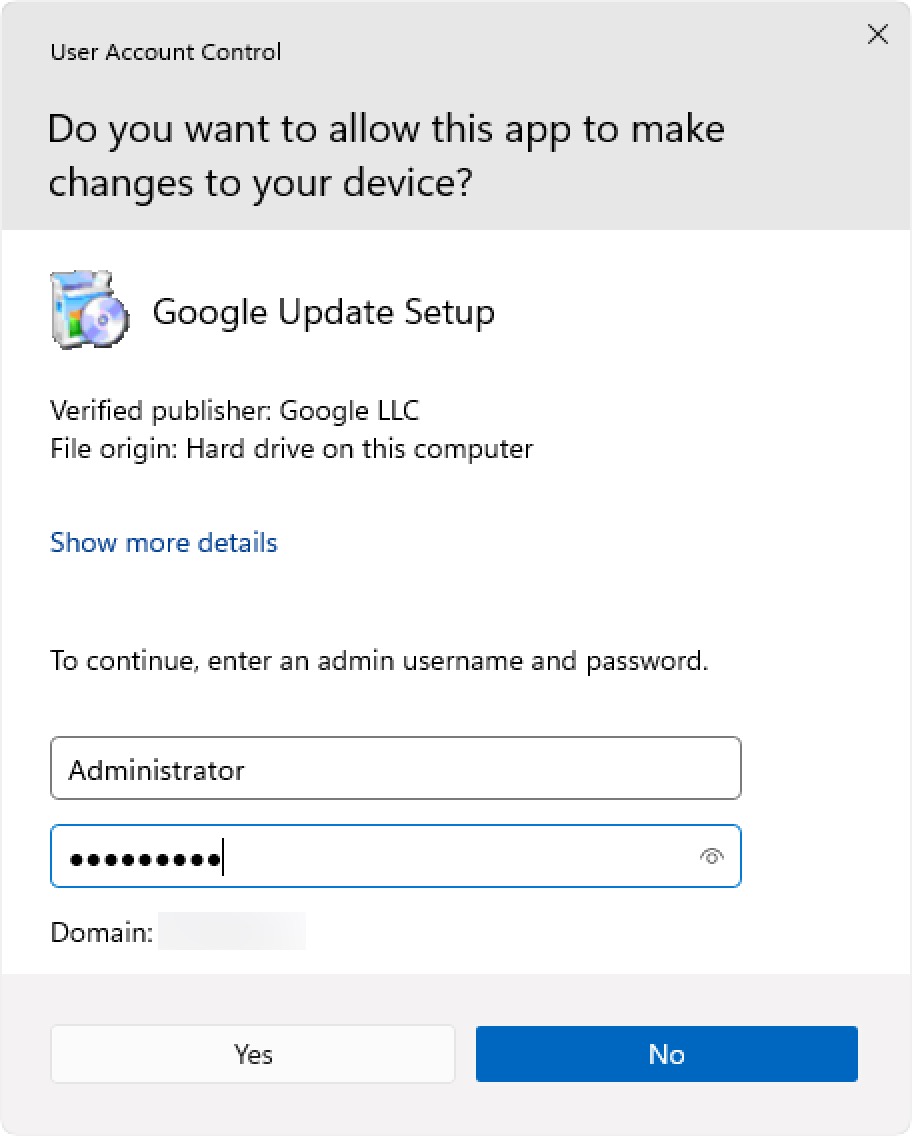
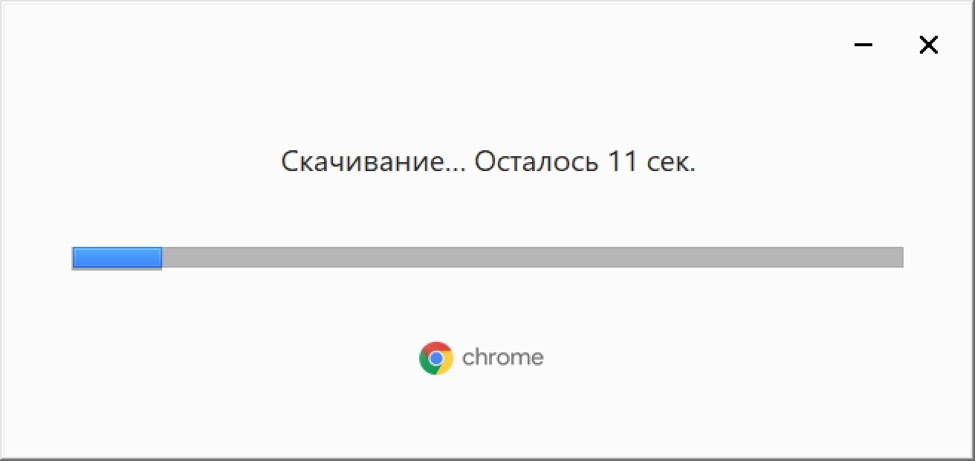
In addition to Steelray Project Viewer files, the EXE installer also installed a Russian version of Google Chrome on my infected lab host. This specific lab host did not previously have Google Chrome (it used Chromium-based Microsoft Edge). The Chrome installation was stopped by UAC, but I bypassed it during the infection run. Of note, I was running an English version of Windows from a US IP address.
- Shown above: UAC stops the Russian version of Google Chrome from automatically installing.
- Shown above: Russian version of Google Chrome installing after bypassing UAC.
- Shown above: Russian version of Google Chrome after installation.
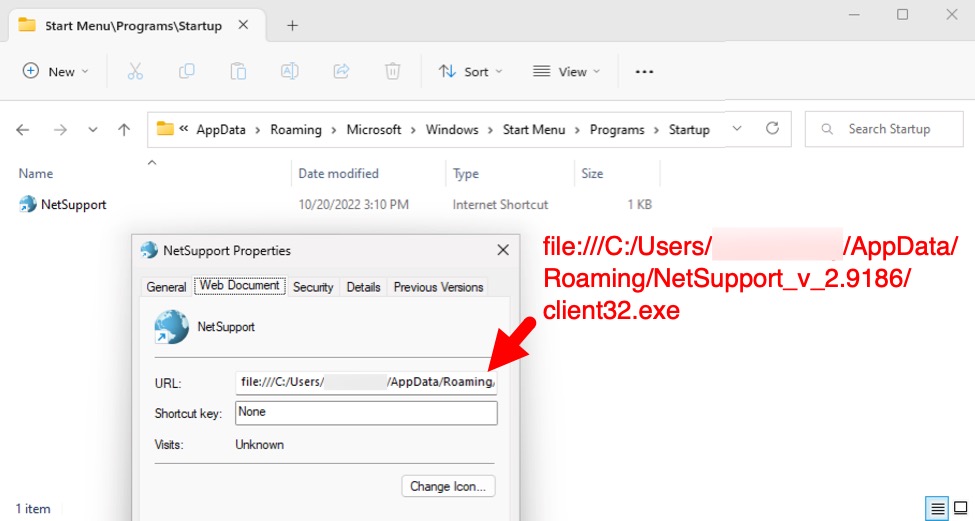
- Shown above: URL shortcut in startup menu folder to keep NetSupport RAT persistent.
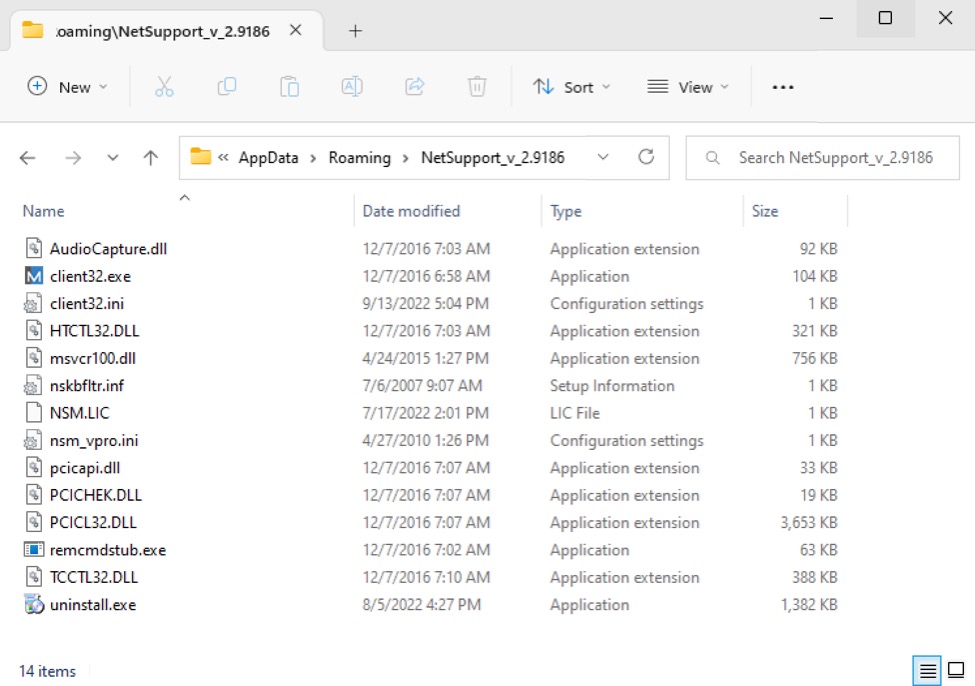
- Shown above: Files for Netsupport Manager RAT on the infected Windows host.
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments