Monster Libra (TA551/Shathak) pushes IcedID (Bokbot) with Dark VNC and Cobalt Strike
Introduction
Since 2019, threat actor Monster Libra (also known as TA551 or Shathak) has pushed different families of malware. During the past few months, Monster Libra has primarily pushed SVCready or IcedID. Today's diary reviews an example of Monster Libra pushing IcedID on Thursday 2022-08-11, and that IcedID infection led to Dark VNC activity and Cobalt Strike.
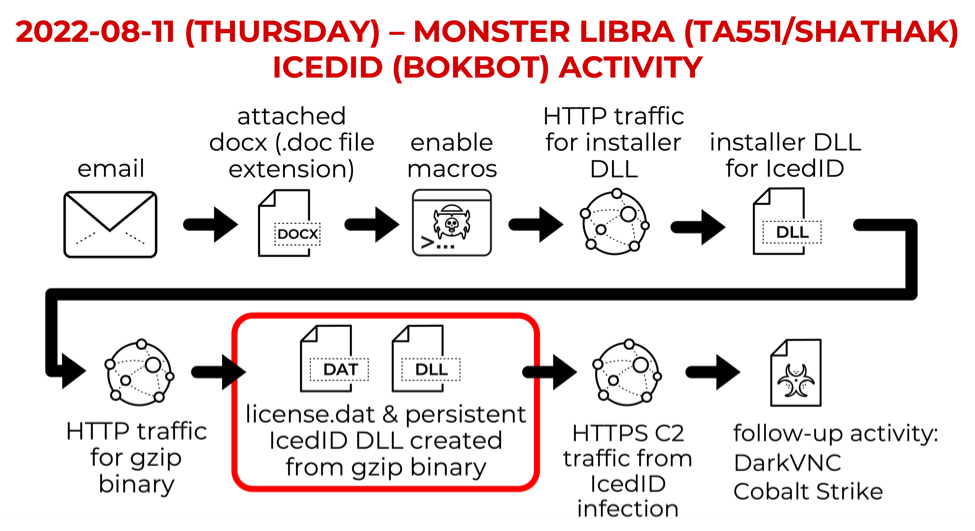
Shown above: Chain of events for IcedID infection distributed through Monster Libra.
Images From the Infection
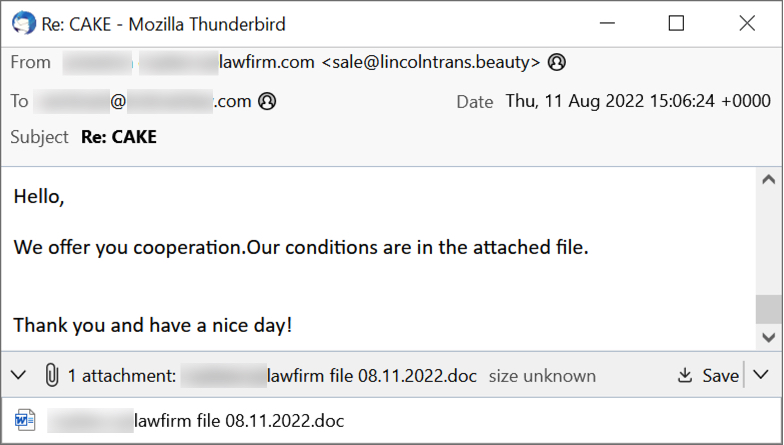
Shown above: Screenshot of a Monster Libra email.
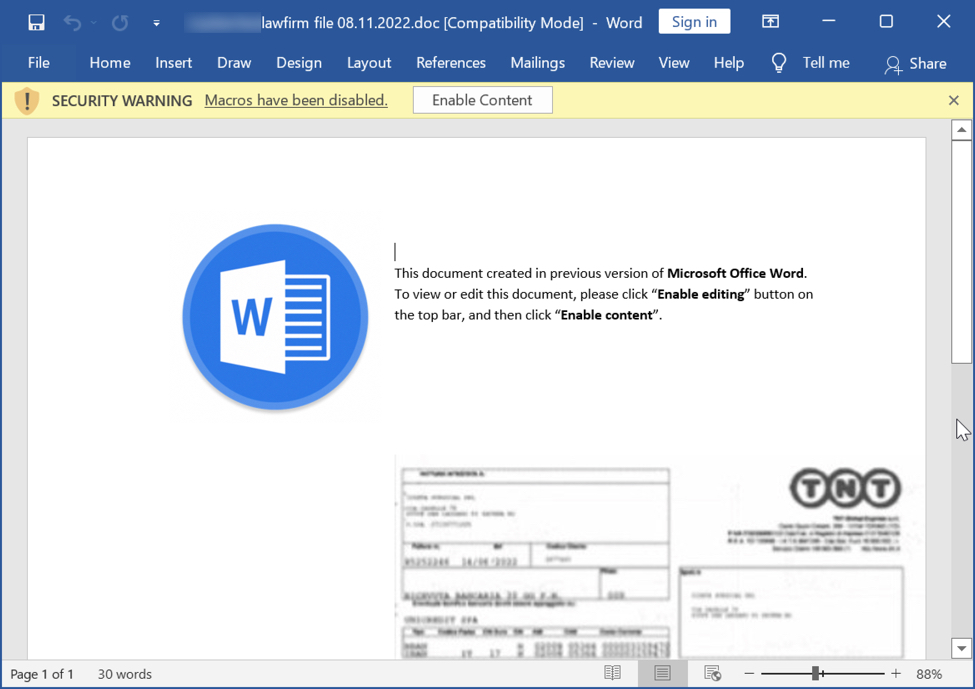
Shown above: Screenshot of the attached Word document.
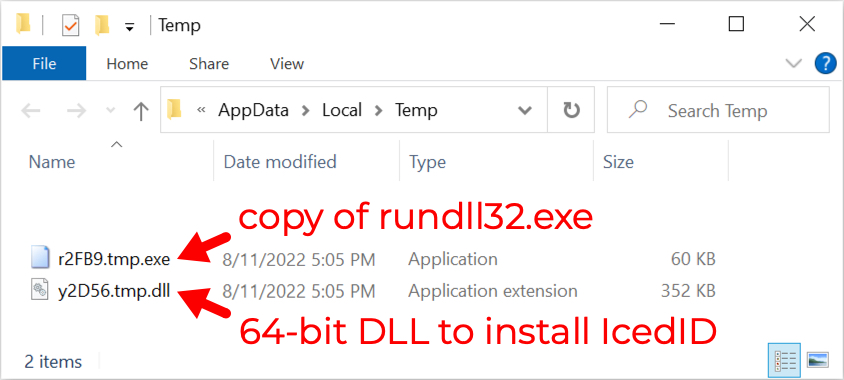
Shown above: Files that appeared after enabling macros
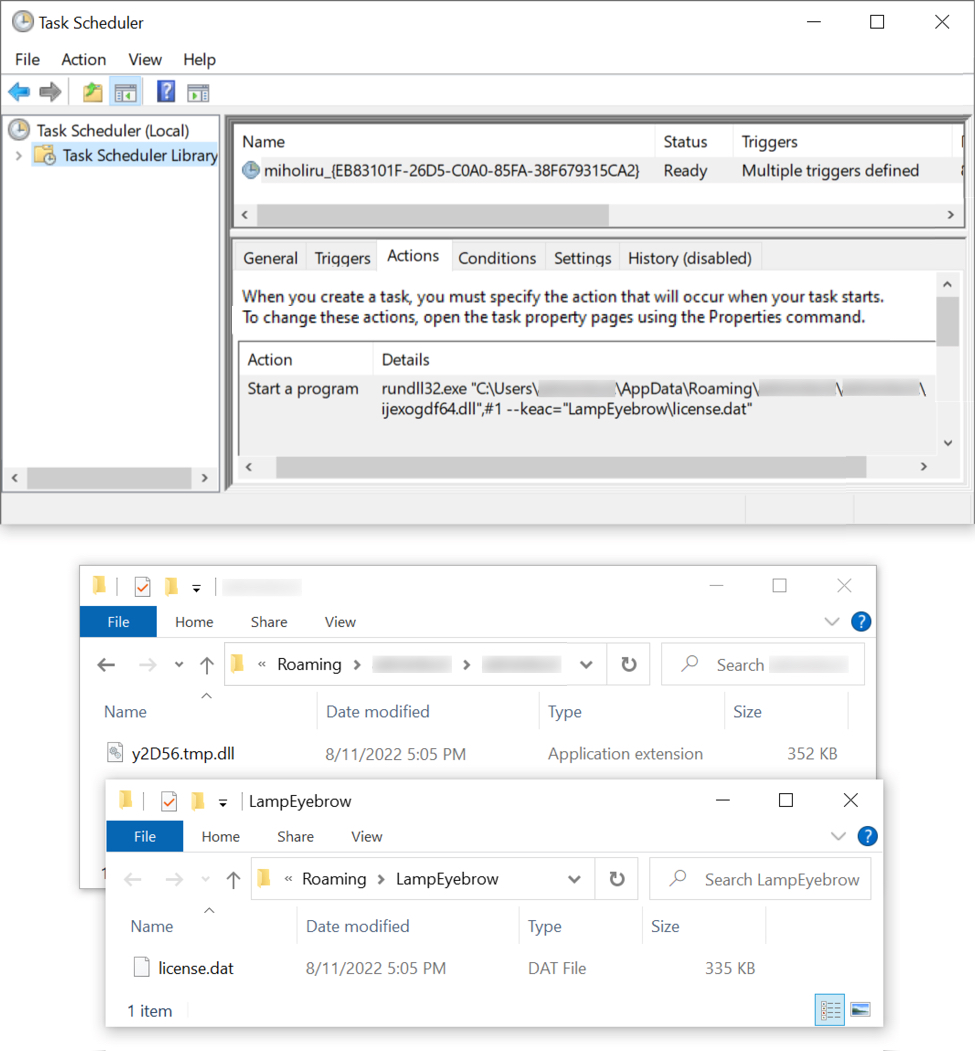
Shown above: Scheduled task for persistent IcedID infection.
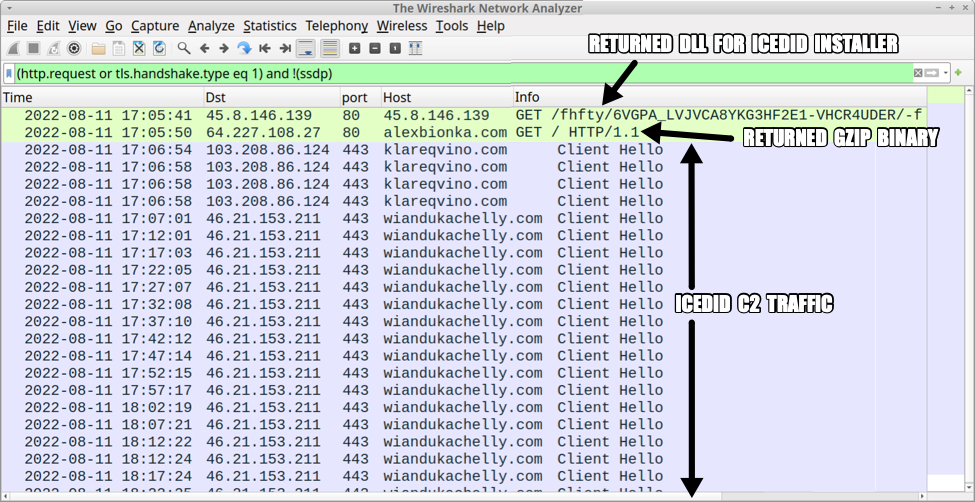
Shown above: Traffic from an infection filtered in Wireshark (image 1 of 2).
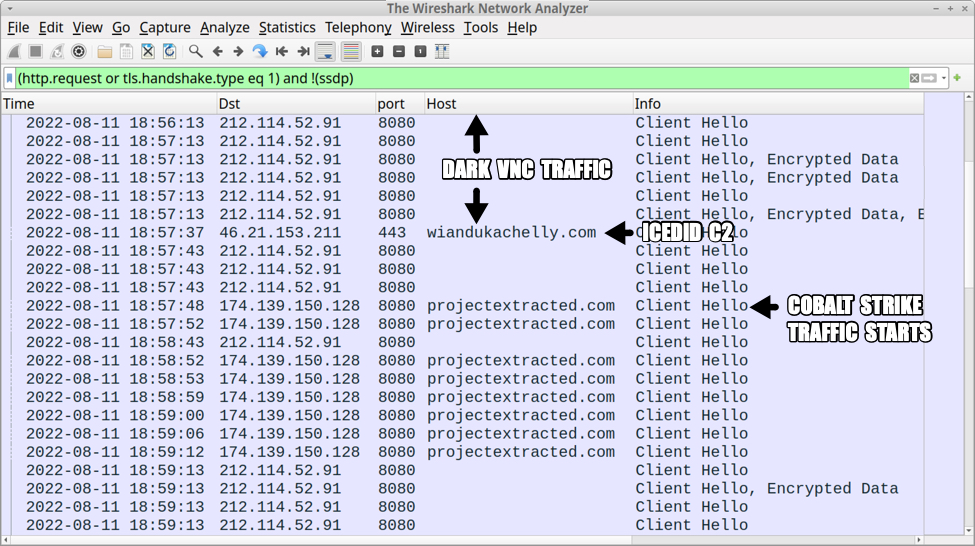
Shown above: Traffic from an infection filtered in Wireshark (image 2 of 2).
Indicators of Compromise (IOCs)
20 Word docs found on VT:
- 2,316,894 bytes - [name removed] doc 08.11.2022.doc
- 2,343,230 bytes - [name removed] doc 08.11.2022.doc
- 2,349,822 bytes - [name removed] doc 08.11.doc
- 2,316,250 bytes - [name removed] file 08.11.2022.doc
- 2,365,937 bytes - [name removed] file 08.11.22.doc
- 2,298,962 bytes - [name removed] invoice 08.11.22.doc
- 2,343,139 bytes - [name removed],doc,08.11.22.doc
- 2,365,983 bytes - [name removed],document,08.11.22.doc
- 2,298,458 bytes - [name removed],file,08.11.2022.doc
- 2,298,562 bytes - [name removed],file,08.11.22.doc
- 2,297,841 bytes - [name removed]-doc-08.11.2022.doc
- 2,350,727 bytes - [name removed]-invoice-08.11.22.doc
- 2,315,700 bytes - [name removed].doc.08.11.22.doc
- 2,316,502 bytes - [name removed].document.08.11.2022.doc
- 2,316,883 bytes - [name removed].document.08.11.2022.doc
- 2,316,402 bytes - [name removed].invoice.08.11.2022.doc
- 2,351,271 bytes - [name removed]doc08.11.doc
- 2,366,716 bytes - [name removed]document08.11.22.doc
- 2,298,836 bytes - [name removed]document08.11.doc
- 2,349,614 bytes - [name removed]file08.11.22.doc
SHA256 hashes of the 20 Word docs:
- 025d824f7fd062715efe4914065eb6026a0f1720256f03e18c652978ec9d6844
- 04042893124fdbf007cfdb673ef878ac9a47f37f871c1e5322ec46945915abc1
- 23b9a20a59041fc7d484957e49ffa7e0f6dba7dbbec0628a4adb69c2e05863ab
- 373856a75b78406d26cfbb41cbbba7041bad1e56a3304ba17376b294bc773eee
- 3af042bd0b5a186b98920cf0b7066344609d6d6deb163ffb0b60325dcca66e44
- 3b86f8aff12d2b32461a0b20f01f3d13ee062c80cb647ce09ff33f296b1f9e47
- 3c59aab375e8ebf7a3da914e7f1f38c6c54947b4c27c73c5c591ab27152dfe4d
- 4f479dc5b981aadc01b1f245d8694b1ad043247f04148bbb78a86c8ed530b777
- 500b85d4e573f6e14e96c0a06e2d8fe15572c0eb97e3cc6d204d3416140d8a61
- 565c2dc637cfa658a2bf8263da58aac2492119ea8bfc4287742a34e3ef456f6f
- 78c296d80214d887820a3c55bc06fbc42b17db90fb01aef0766365b383f1e7f1
- 7ed7f3591ed5a7db3e12df16c9625bdc0367ebd5d6aab6d83a98bd5e40bf288f
- 9cb01729327bd958e32aa9481d5a81303627ab7a59b9ae134fb6600ef4e5b680
- aabc9295e27a673dcfb902960b8196a561923cef78ddb061956cb627fcfa782c
- abc8d1097f0249c749f2c7d7058be1b39c88e21d26d45d76985c989289565214
- bc45389ee9779bf1c6ad66d8b25b4032212fbd5db0defd2e5443a27c1b7a4e80
- bcd1525b0a107b809deb7cce89ae7b873681c14f3513d930b63f2b8739c76c4d
- d297f78ca4fc35e899792260c98f752947f7d6b5999650a6210f4a8538a2e655
- d66a64e64a1d1b44ebcc854f04b1e175ccc93b61fff0f093394f6dcdcd785d82
- e9258541a5c96fcacb6a2ce349282db7e9403a16fa9f952e8f1f69929dda7abc
Files from an infected Windows host:
SHA256 hash: 6cbe0e1f046b13b29bfa26f8b368281d2dda7eb9b718651d5856f22cc3e02910
- File size: 61,440 bytes
- File location: C:\Windows\SysWOW64\rundll32.exe
- File location: C:\Users\[username]\AppData\Local\Temp\r2FB9.tmp.exe
- File description: Copy of legitimate Microsoft system file rundll32.exe. This is not inherently malicious.
SHA256 hash: 8cd135e5b49d16aceb7665b6316cd4df2e132ef503ff0af51c080bad7010efd6
- File size: 360,448 bytes
- File location: hxxp://45.8.146[.]139/fhfty/6VGPA_LVJVCA8YKG3HF2E1-VHCR4UDER/-f
- File location: C:\Users\[username]\AppData\Local\Temp\y2D56.tmp.dll
- File description: 64-bit DLL to install IcedID retrieved by Word macro
- Run method: rundll32.exe [filename],#1
SHA256 hash: 5af2d2e245b36447fffff463b66164807f505dc9efcbe7fadfe4d450b1715c46
- File size: 688,572 bytes
- File location: hxxp://alexbionka[.]com/
- File description: gzip from alexbionka[.]com, used to create license.dat and persistent IcedID DLL
SHA256 hash: 1de8b101cf9f0fabc9f086bddb662c89d92c903c5db107910b3898537d4aa8e7
- File size: 342,218 bytes
- File name: C:\Users\[username]AppData\Roaming\LampEyebrow\license.dat
- File description: Data binary used to run persistent IcedID DLL
SHA256 hash: d45c78fa400b32c11443061dcd1c286d971881ddf35a47143e4d426a3ec6bffd
- File size: 345,600 bytes
- File name: C:\Users\[username]\AppData\Roaming\[username]\[username]ijexogdf64.dll
- File description: Persistent 64-bit DLL for IcedID
- Run method: rundll32.exe [filename],#1 --keac="[path to license.dat]"
Note: No binaries were saved to disk for DarkVNC or Cobalt Strike.
Traffic for IcedID installer DLL:
- hxxp://45.8.146[.]139/fhfty/6VGPA_LVJVCA8YKG3HF2E1-VHCR4UDER/-f
Traffic for gzip binary:
- 64.227.108[.]27:80 - alexbionka[.]com - GET / HTTP/1.1
IcedID C2 activity:
- 103.208.86[.]124:443 - klareqvino[.]com - HTTPS traffic
- 46.21.153[.]211:443 - wiandukachelly[.]com - HTTPS traffic
- 84.32.188[.]164:443 - ultomductingbig[.]pro - HTTPS traffic
DarkVNC activity:
- 212.114.52[.]91:8080 - encoded/encrypted TCP traffic
Cobalt Strike activity:
- 174.139.150[.]128:8080 - projectextracted[.]com - HTTPS traffic
Final Words
IcedID continues to be an active malware in our current threat landscape. Threat actors like Monster Libra continue to push IcedID through malspam-based campaigns as described in this diary. We expect to find more of this activity in the coming weeks.
Brad Duncan
brad [at] malwre-traffic-analysis.net


Comments