Analyzing a Phishing Word Document
Reader Bob submitted a malicious Word document.
According to the filename (Payments & Receipt.docx), it's a .docx file: an OOXML file without VBA macros.
Nevertheless, I often take a first look at Office maldocs with my tool oledump.py. Because the file might still contain OLE files (for embedded files, for example) and because oledump.py will also tell me if it is indeed an OPC file (OOXML is based on OPC).
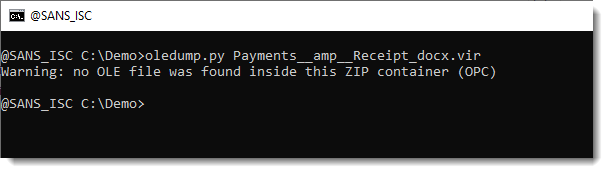
So no OLE file was found inside, and it is indeed an OPC file.
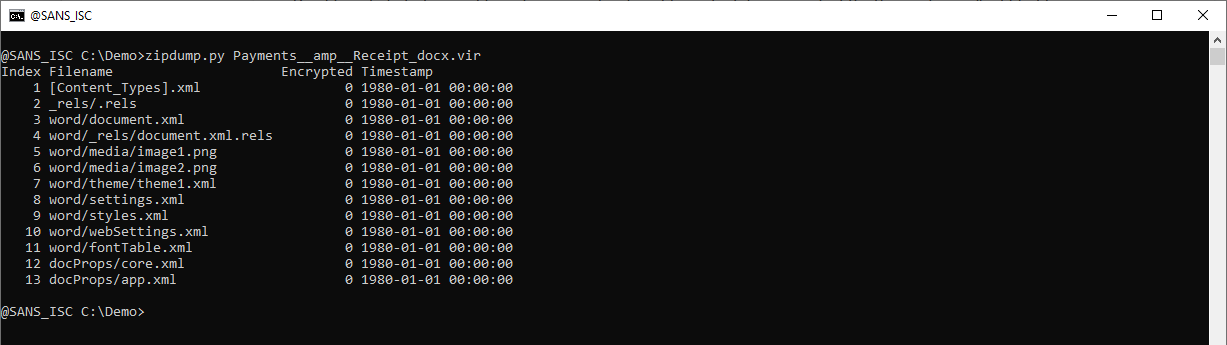
Next I take a look with zipdump.py:
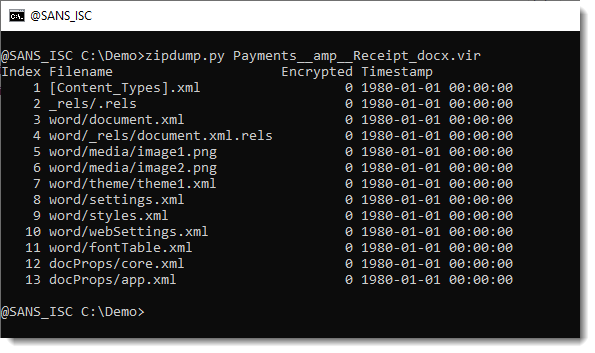
Besides the 2 PNG files, it looks like there are only XML files inside. And the timestamps are all 1980-01-01, exactly what it should be for an OOXML file created with Office. It contains a word/document.xml file, so it's very likely a .DOCX file.
Next, when I see no embedded VBA macros or unusual files in an OOXML Word document, I look for unusual URLs.
The XML files inside OOXMl files contain a lot of URLs (referencing standards), so it's best to filter these expected URLs out. I dump the content of all files inside the OOXML to stdout (zipdump.py -D) and pipe this into re-search.py, my tool to look for particular patterns using regular expressions. Option -n url selects a regular expression for URLs, option -u removes duplicates, and option -F officeurls removes all URLs with domains that are common in XML standard references.
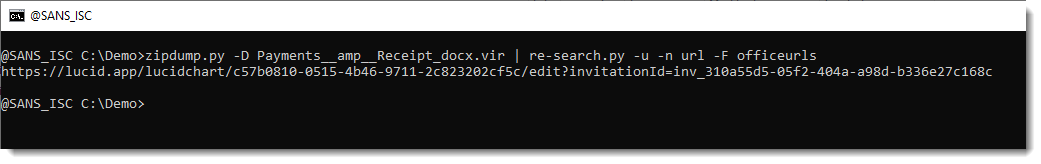
And there is one unusual URL.
Notice that re-search searches inside text files. It can search into binary files too, but then you need to use option -e so that it can extract strings
If you want to know in which file this URL is stored, you can run an ad-hoc yara search for a distinctive part of the URL:
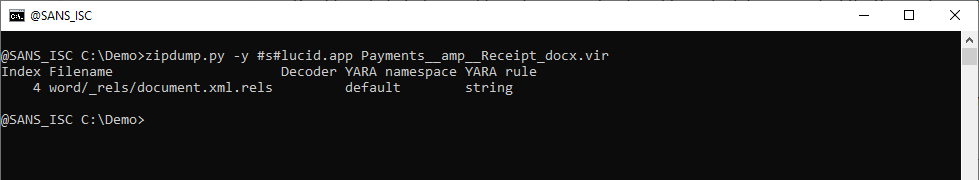
It's in the relationships file:
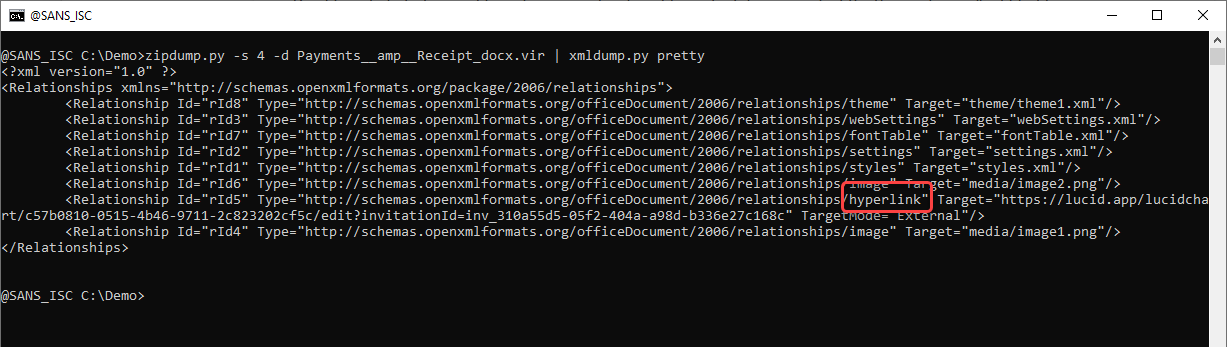
And it is a hyperlink. So this is a phishing document. We can look at the text in the Word document like this with xmldump.py:
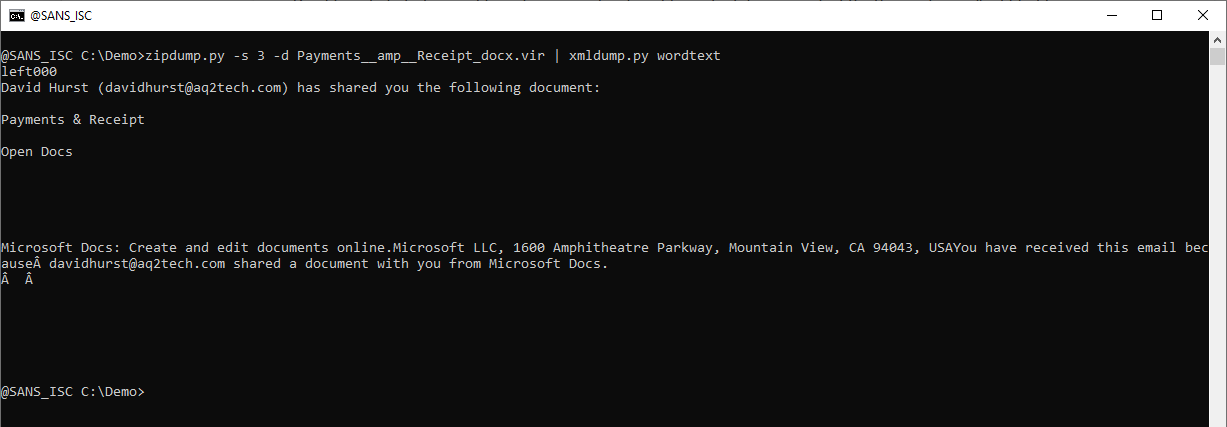
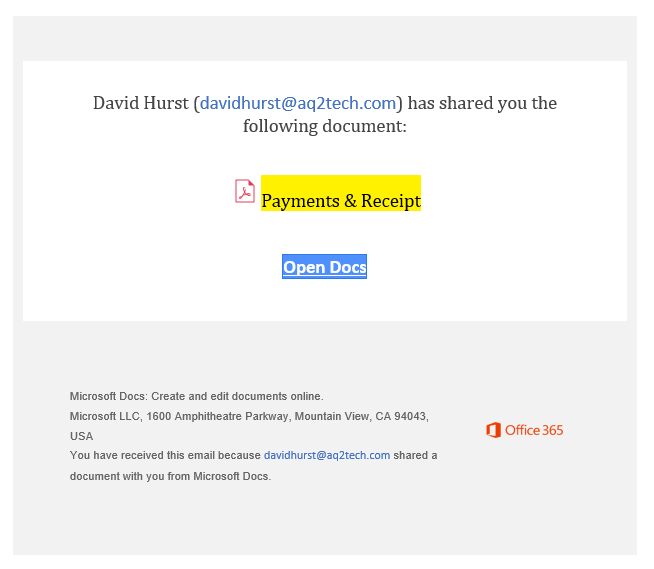
And here is the document itself:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com


Comments