TShark & Multiple IP Addresses
In diary entry "TShark & jq", I mention that a single packet can have more than one ip.src entry.
I will illustrate this here. We are looking at a capture of network traffic where TCP SYN packets can not be delivered: "Destination unreachable".
Here is the view with TShark:
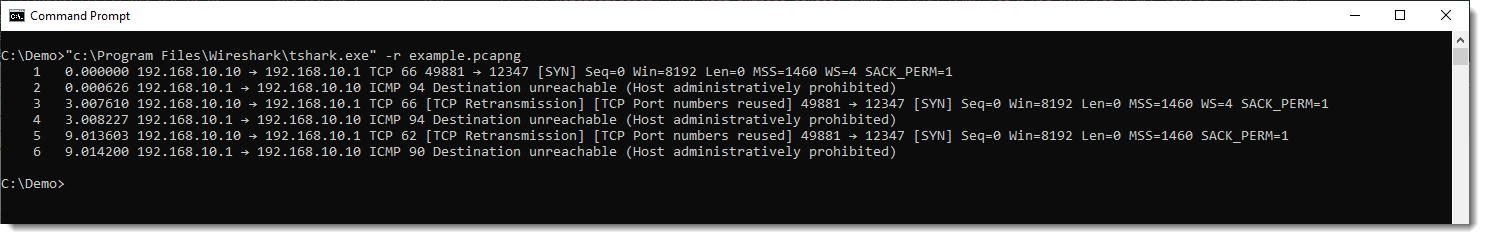
Notice TCP packets going from 192.168.10.10 to 192.168.10.1, and ICMP packets going from 192.168.10.1 to 192.168.10.10.
If we run a TShark command to extract all ip.src values, we get this:
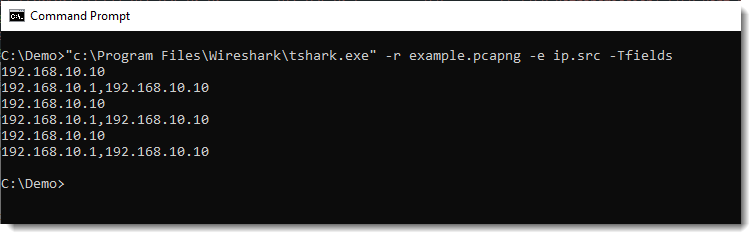
For ICMP packets, we have 2 IPv4 addresses for the ip.src field: 192.168.10.1 and 192.168.10.10.
This is happening, because the ICMP packet embeds the IP packet to which it is replying. You can see this here in Wireshark:
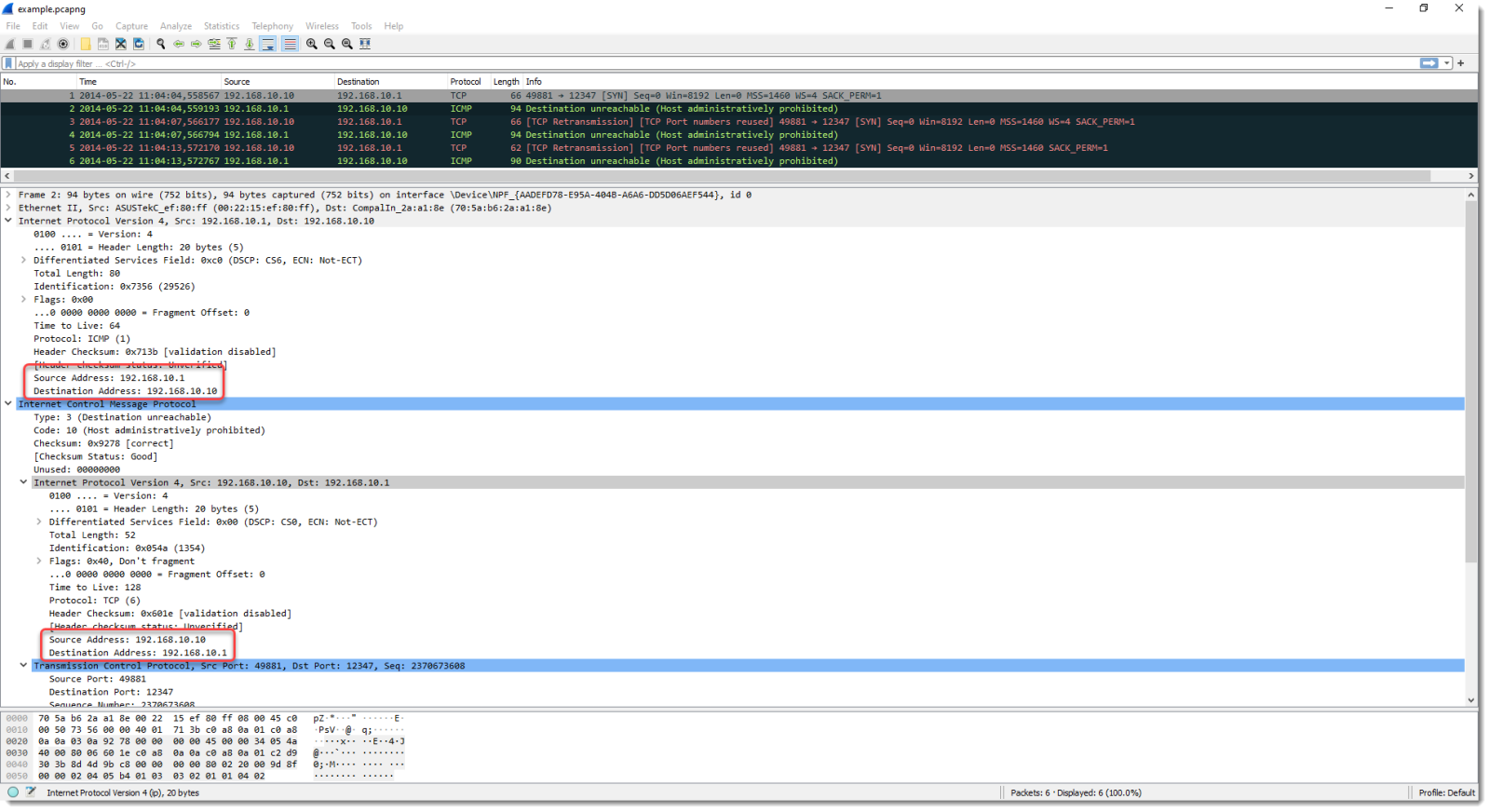
The ICMP packet, encapsulated in an IP packet, has ip.src value of 192.168.10.1.
But it also embeds the IP packet (with TCP) to which it is replying. That one has a src.ip value equal to 192.168.10.10.
These are different fields, but both are accessed via ip.src and yield different values.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com



Comments