PuTTY And FileZilla Use The Same Fingerprint Registry Keys
Many SSH clients can remember SSH servers' fingerprints. This can serve as a safety mechanism: you get a warning when the server you want to connect to, has no longer the same fingerprint. And then you can decide what to do: continue with the connection, or stop and try to figure out what is going on.
This happened to me a couple of months ago. I wanted to transfer some files over SSH with FileZilla, and received a prompt that the server I usually connect to, had an unknown fingerprint. I did not go through with the connection, and started to investigate what was going on.
Long story short: I had removed SSH fingerprints cached by PuTTY in the Windows registry, and this impacted FileZilla: both use the same registry keys for their fingerprint cache.
You can see the registry keys here in FileZilla's source code:
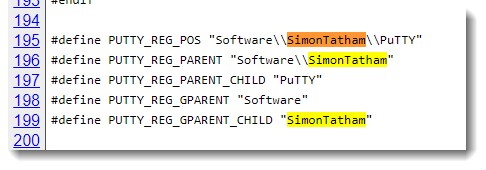
If you do forensics on Windows machines, be aware that these registry keys are not only used by PuTTY, but also by FileZilla's fzsftp.exe module.
I have more details here if you are interested.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments