Secure Communication using TLS in Elasticsearch
In the past, I have published a couple diaries on Elasticsearch for pihole and tcp-honeypot to parse and report on the data capture by those applications.
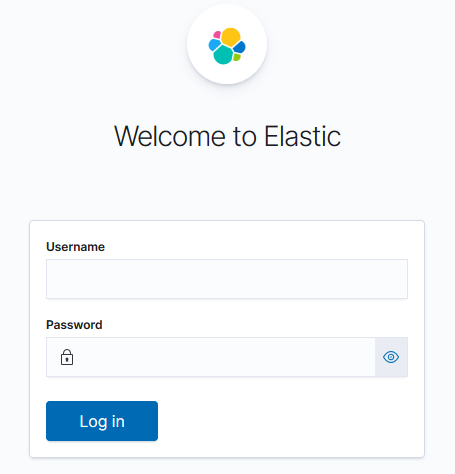
This document is a compilation of the various references listed in the PDF document (here as well), it documents step-by-step the processes I have been using to setup TLS encryption within my test network. Using Elasticsearch elasticsearch-certutil tool in CA mode, it simplifies the creation of certificates and generates a new certificate authority (CA) to use within the local ELK infrastructure. These steps provide secure communication for Linux and Windows between Elasticsearch nodes, Kibana, logstash and the various beats.
The complete installation document TLS_elasticsearch_configuration.pdf can be viewed here.
[1] https://handlers.sans.edu/gbruneau/elk/TLS_elasticsearch_configuration.pdf
[2] https://isc.sans.edu/forums/diary/ELK+Dashboard+for+Pihole+Logs/25652/
[3] https://isc.sans.edu/forums/diary/ELK+Dashboard+and+Logstash+parser+for+tcphoneypot+Logs/25702/
[4] https://www.elastic.co/guide/en/elasticsearch/reference/current/configuring-tls.html
[5] https://www.elastic.co/guide/en/elasticsearch/reference/current/certutil.html
[6] https://www.elastic.co/blog/configuring-ssl-tls-and-https-to-secure-elasticsearch-kibana-beats-and-logstash
[7] https://www.elastic.co/guide/en/elasticsearch/reference/master/encrypting-communications-certificates.html
[8] https://www.elastic.co/blog/elasticsearch-security-configure-tls-ssl-pki-authentication
[9] https://techexpert.tips/elasticsearch/elasticsearch-enable-tls-https/
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments