VBA Project Passwords
A VBA project can be protected with a read-password: a password you need to enter in order to be able to view and edit the VBA project in the VBA IDE.
I've never gave much attention to documents with password protected VBA code, because it's just that: a protection, enforced by the IDE. The VBA code itself is not encoded or encrypted, you can view it with my tool oledump.py or Philippe's tool olevba.py without any problem. In fact, you won't even notice that it is password protected if you use our tools.
To see with my tool if a VBA project is password protected, you take a look at the PROJECT stream. This stream is pure text, structured like an INI file. You will find an ID entry, usually the first line, with a GUID as value. This GUID is unique per VBA project, unless the VBA project is password protected. A password protected VBA project has a "NULL" GUID: ID="{00000000-0000-0000-0000-000000000000}"
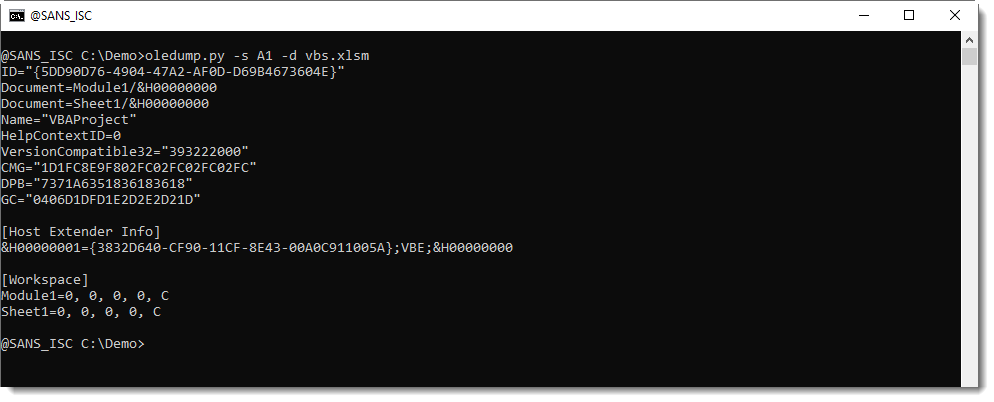
Here is an example of the PROJECT stream of a VBA project without password:
And here is an example of the PROJECT stream of a VBA project with password:
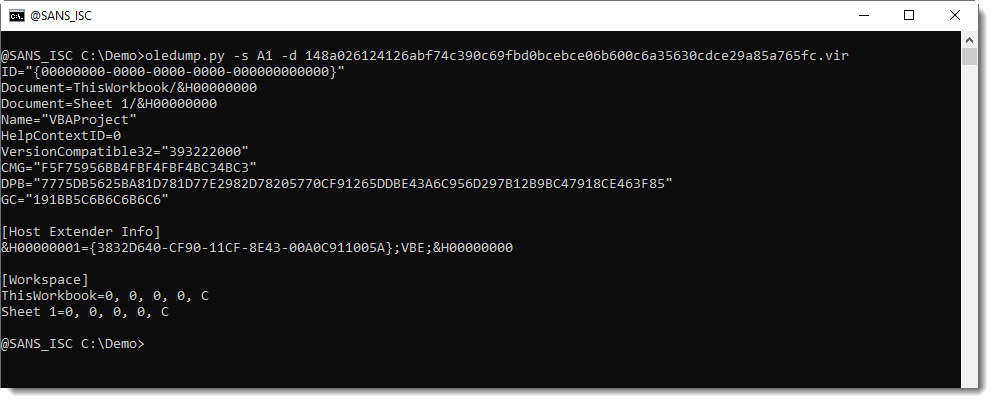
Notice that entry DPB (ProjectPassword) is longer: that's because this ID contains the hash of the password. All this is explained in MS-OVBA 2.3.1.16.
I've never tried to crack password hashes like these, because the VBA code is not encoded/encrypted when a password is set. And if you want to remove the password, you can take the ID, DPB, CMG and GC entries of a VBA project without password, and use them as replacement values in the password protected VBA project.
But if you would happen to know of a free open-source tool to crack VBA project passwords (i.e recover the password, not remove it), please post a comment.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments