Maldoc: Excel 4 Macros in OOXML Format
I've mentioned Excel 4 macros before, a scripting technology that predates VBA.
In that diary entry, I handle .xls files (ole files). Excel 4 macros can also be stored in Office Open XML format files: .xlsm files.
If we take a look at an .xlsm file with Excel 4 macros with oledump.py, we'll get this output:
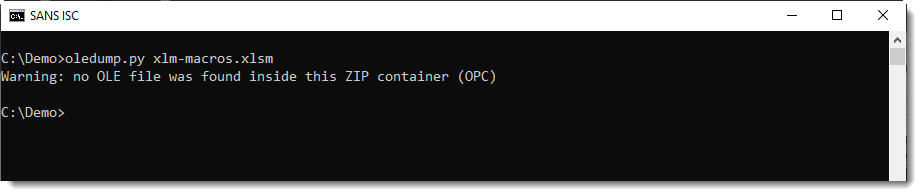
There is no ole file (vbaProject.bin) file inside an Excel 4 macro-only file.
We need to take a look with zipdump.py:
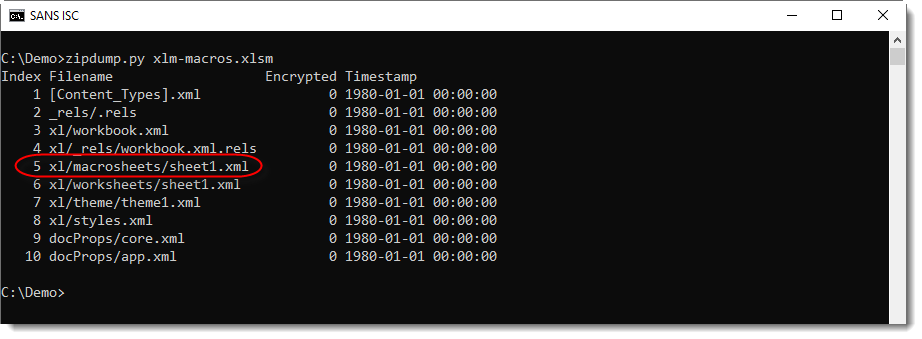
The presence of folder macrosheets tells us that there are Excel 4 macro sheets inside this file.
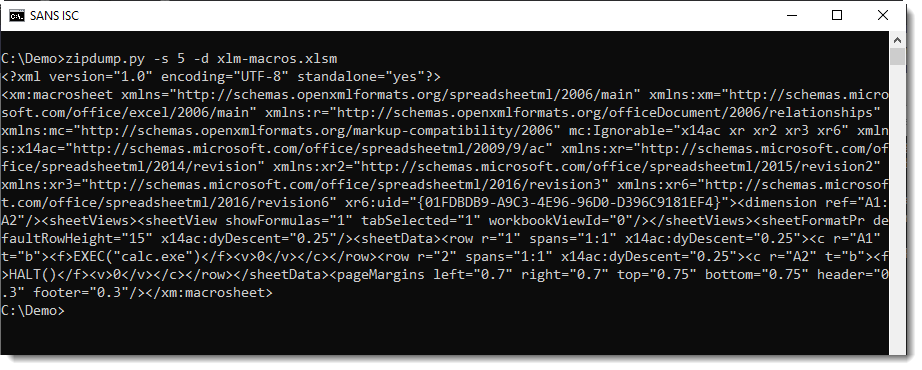
We can look at the content of the XML file:
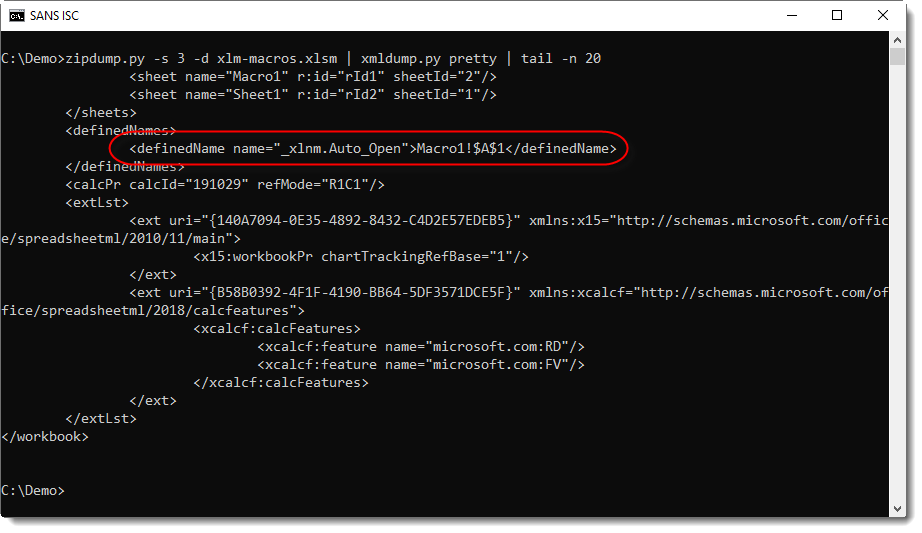
And pretty-print it with xmldump.py:
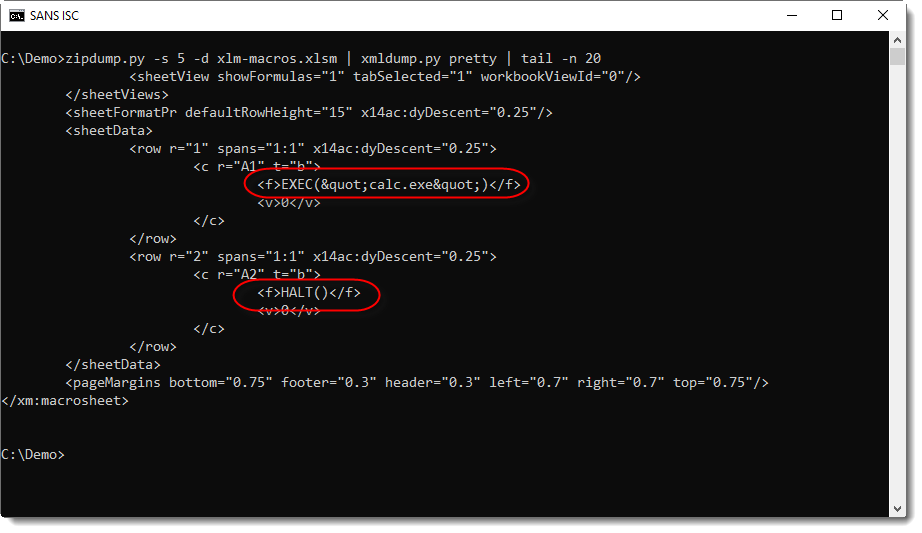
Now it's easier to spot the formulas: EXEC("calc.exe") and HALT()
And the Auto_Open can be found in the worksheet XML file:
It's possible to have both macro types inside the same file: Excel 4 and VBA macros. I'll cover that in an upcoming diary entry.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments