curl and SSPI
There's an interesting comment on Xavier's diary entry "Keep an Eye on Command-Line Browsers" (paraphrasing): a proxy with authentication will prevent wget and curl to access the Internet because they don't do integrated authentication.
It just happens that since a couple of months, I use curl on Windows with SSPI to authenticate to a proxy. I use the following command:
curl --proxy proxyname:proxyport --proxy-ntlm -U : https://isc.sans.edu
First, you need a version of curl with SSPI support:
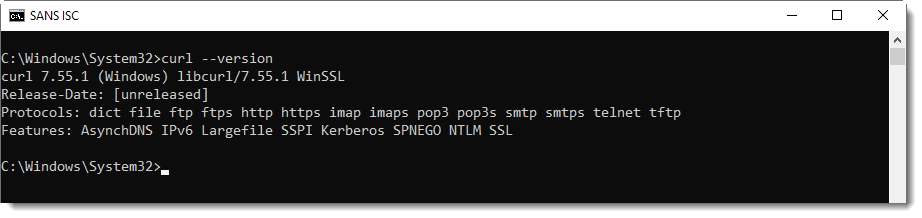
Windows 10's version of curl does support SSPI.
With this, I can connect to my proxy (--proxy) and authenticate (--proxy-ntlm) without having the provide credentials to authenticate to the proxy (-U :). curl will use an SSPI to perform integrated authentication to the proxy. This is explained on curl's man page:
If you use a Windows SSPI-enabled curl binary and do either Negotiate or NTLM authentication then you can tell curl to select the user name and password from your environment by specifying a single colon with this option: "-U :".
curl's SSPI feature can also be used to authenticate to an internal IIS server.
By default, curl will not authenticate to a proxy, but it can be directed to do so via options.
I didn't find a version of wget that supports SSPI. If you know one, or you made one, please post a comment.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments