etl2pcapng: Convert .etl Capture Files To .pcapng Format
Over the holidays, I wanted to look into a packet capture file I created on Windows with a "netsh trace" command. Such an .etl file created with a "netsh trace" command can not be opened with Wireshark, you have to use Microsoft Message Analyzer.
When I wanted to make sure that I still had the latest version of Microsoft Message Analyzer (I have version 1.4), I discovered that Microsoft Message Analyzer has been retired and the downloads have been removed from Microsoft's sites.
I continued to search on the Internet for more information, and I came across a new utility: etl2pcapnp. It's a "Utility that converts an .etl file containing a Windows network packet capture into .pcapng format". It's a Windows program, and it's open source.
etl2pcapng is a command-line utility taking 2 arguments: input file (.etl) and output file (.pcapng):
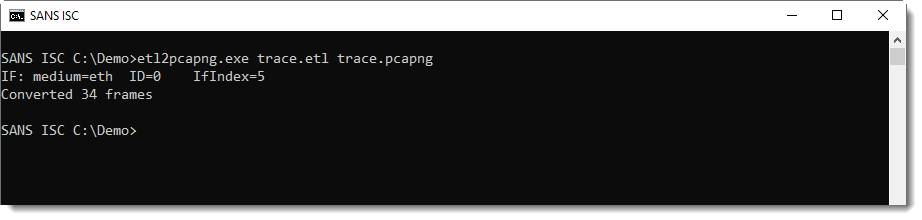
And then you can open that .pcapng file with Wireshark, or any other tool that supports .pcapng files.
In an upcoming diary entry, I'll talk about a change I made to the source code.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments