Fake Office 365 Payment Information Update
If you currently have Office 365, watch out for fake request with a Subject of "Action required: Update your payment information now" and with sender: "Microsoft Online Services Team no-replay@support.onmicrosoft.com". Over the past few weeks I have received several of these emails which looks quite legitimate. Here is an example:
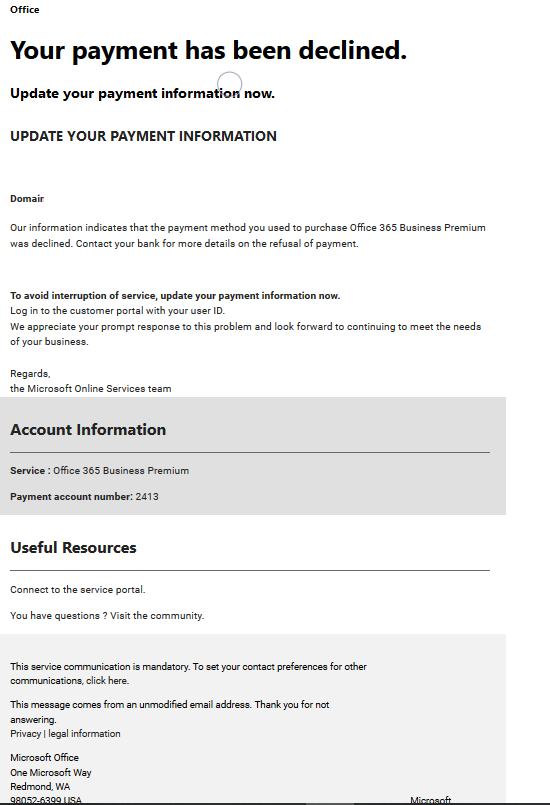
However, a quick review of the embedded URL shows this is spam if your email program didn't already categorize it as such [1]. The URL is no longer active but domain offene-tueren.net (81.169.145.148) tracked by ransomware tracker is associated with Locky malware.
Refer to a recent posting from Microsoft [3] that describes how Office 365 mitigates against phishing attacks. A valid message from Microsoft would look like item #2 "Microsoft account security code".
1. http://login.live.com.login.offene-tueren.net/?Z289MSZzMT0zODYwMjkmczI9OTU3MzE5MTAmczM9R0xC
2. https://ransomwaretracker.abuse.ch/ip/81.169.145.148/
3. https://docs.microsoft.com/en-us/office365/securitycompliance/anti-spoofing-protection
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments