Cisco ASA WebVPN Vulnerability
Before I get too many "I'm surprised/disappointed you haven't mentioned..." emails let's get out a rough draft on CVE-2018-0101.
What is it? A Base CVSS of 10 remote code execution and denial of service vulnerability affecting Cisco ASA devices with webvpn configured with SSL support.
What's the hurry? Details of the exploit research will be presented this weekend at Recon in Brussels. So it's getting some press. Also, CISCO released the advisory yesterday so people who are into that sort of thing are writing their own tests and scanners and exploits.
How do I know if I'm affected? I don't own one of these, so I don't have a great answer. Do you have a CISCO ASA? (check your inventory) Do you have webvpn configured? (check your config) Does it support SSL or is it TLS support only? (check your config)
I have one of these set up this way, now what do I do? Upgrade to the 9.6 branch and patch.
I can't do that for reasons, what do I do? Reduce the exposure by blocking un-needed networks.
Very funny, it's a vpn, I need that open to the Internet. Do you really need it open to the ENTIRE Internet?
Yes, I'm a <industry> and <reasons> Okay, if you can't patch, and you can't block, then you must monitor.
Alright, how do I do that? I'm going to have to get back to you on that. Update: You may want to look at these proposed IDS signatures: https://gist.github.com/fox-srt/09401dfdfc15652b22956b9cc59f71cb
Using FLIR in Incident Response?
Take a look at a few lines...
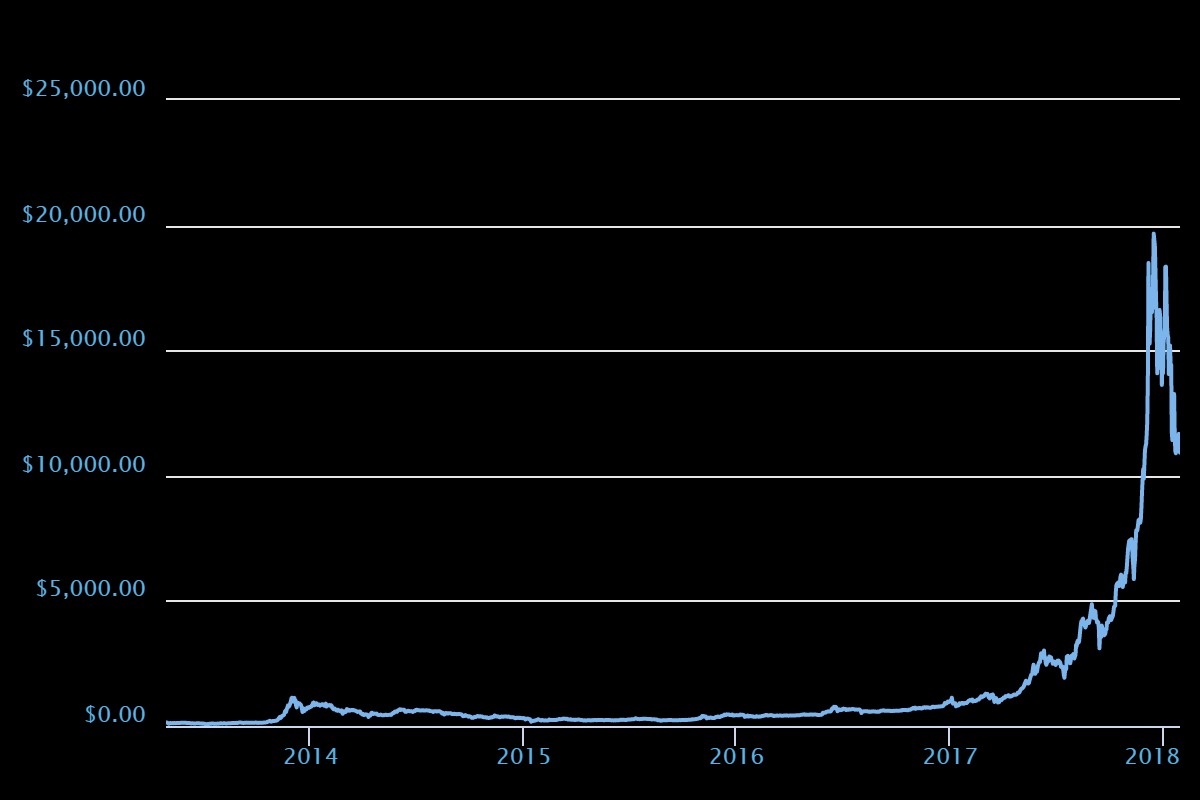
Frist the going rate of a bitcoin:
Next the going rate of monero:
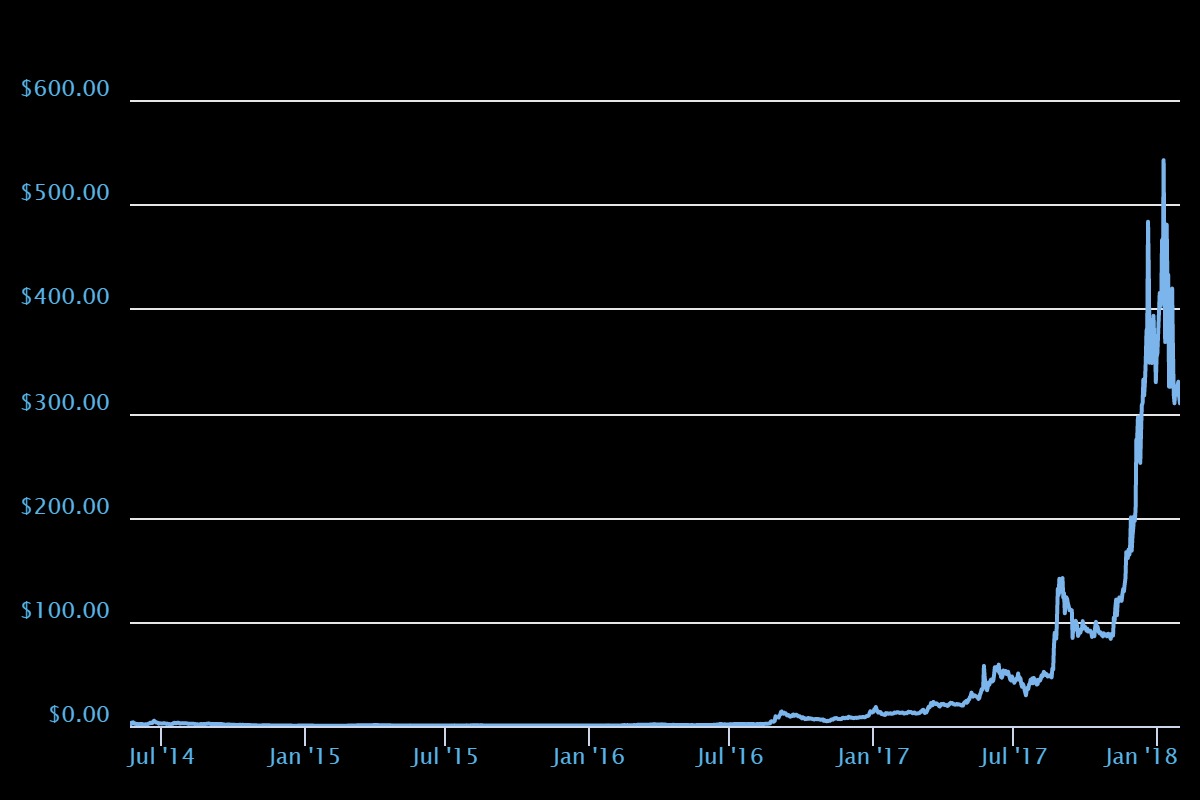
Both are seeing a lot of gains. How is their performance related to each other?
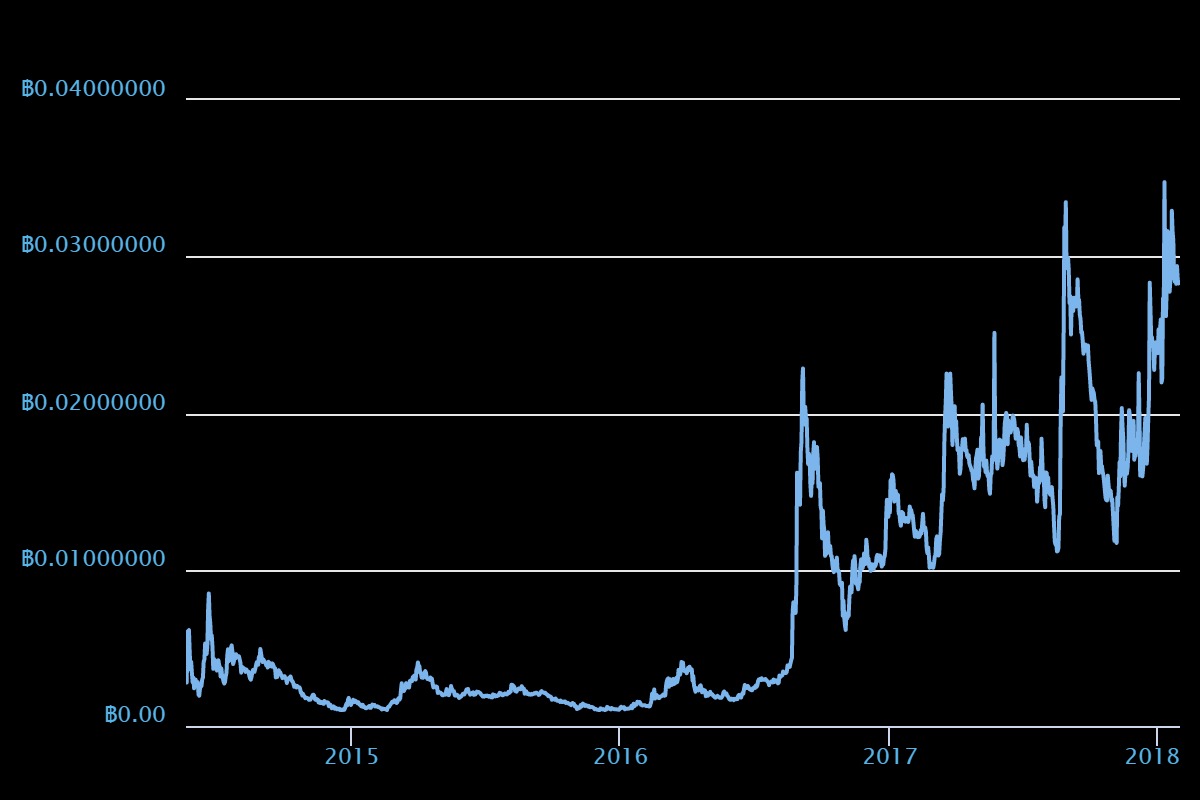
Here are a few more lines to look at...
The Google Webtrends for the search term "ransomware":

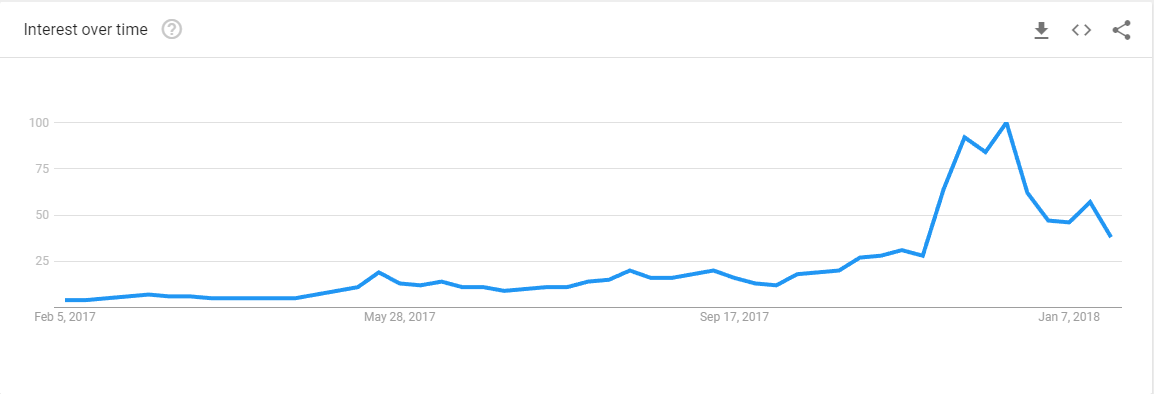
Now the trends for the term "bitcoin":
And the trend for the term "monero":
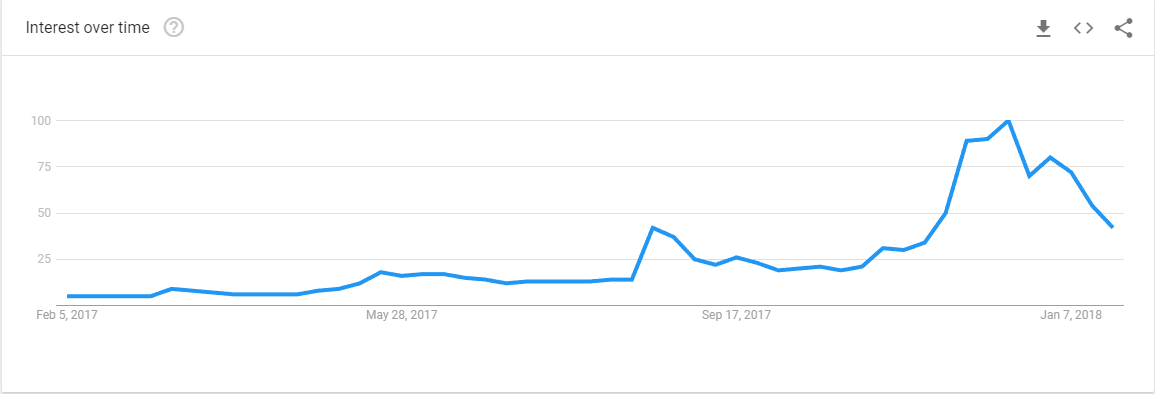
The peak interest in "ransomware" searches is in May 2017 back when Wanacry was making a lot of noise. NotPetya hit in June/July of 2017 and that seems to have been ransomware stopped losing its appeal for criminals. Because NotPetya was a wiper and not actual ransomware, confidence that you would get your files back if you paid the ransom eroded. Ransomware hasn't disppaered, but it has dropped in popularity. (There appears to be more money to be made helping people launch ransomware attacks than actually launching attacks see: https://isc.sans.edu/forums/diary/Ransomware+as+a+Service/23277/)
Perhaps criminals don't want the amount of attention that incidents like wanacry or NotPetya generated. Maybe they feel bad about the unintended consequences of locking down a hospital's computer system? Or maybe there's just more/easier money in finding unused/poorly-secured resources to generate cryptocurrencies.
Crypto miners seem to be the payload du jour. While writing this down, reader Chis shared the miner that was dropped on one of their servers. The ad hoc bash script used indicates that there's a bit of red-on-red violence in the ilicit mining scene. It also seems to be profitable, it looks like the pool used in this instance has generated a dozen or so monero units (is that the right term?) so far.
In response to this trend I'm adding an FLIR camera to my Incident Response jump kit.


Comments