Who's Attacking Me?
I started to play with a nice reconnaissance tool that could be helpful in many cases - offensive as well as defensive. "IVRE" [1] ("DRUNK" in French) is a tool developed by the CEA, the Alternative Energies and Atomic Energy Commission in France. It's a network reconnaissance framework that includes:
- Passive recon features (via flow analysis coming from Bro or Nfdump
- Fingerprinting analysis
- Active recon (via Nmap or Zmap)
- Import tools (from Nmap or Masscan)
I deployed this tool and feed it with attacker's IP addresses collected by my honeypots:
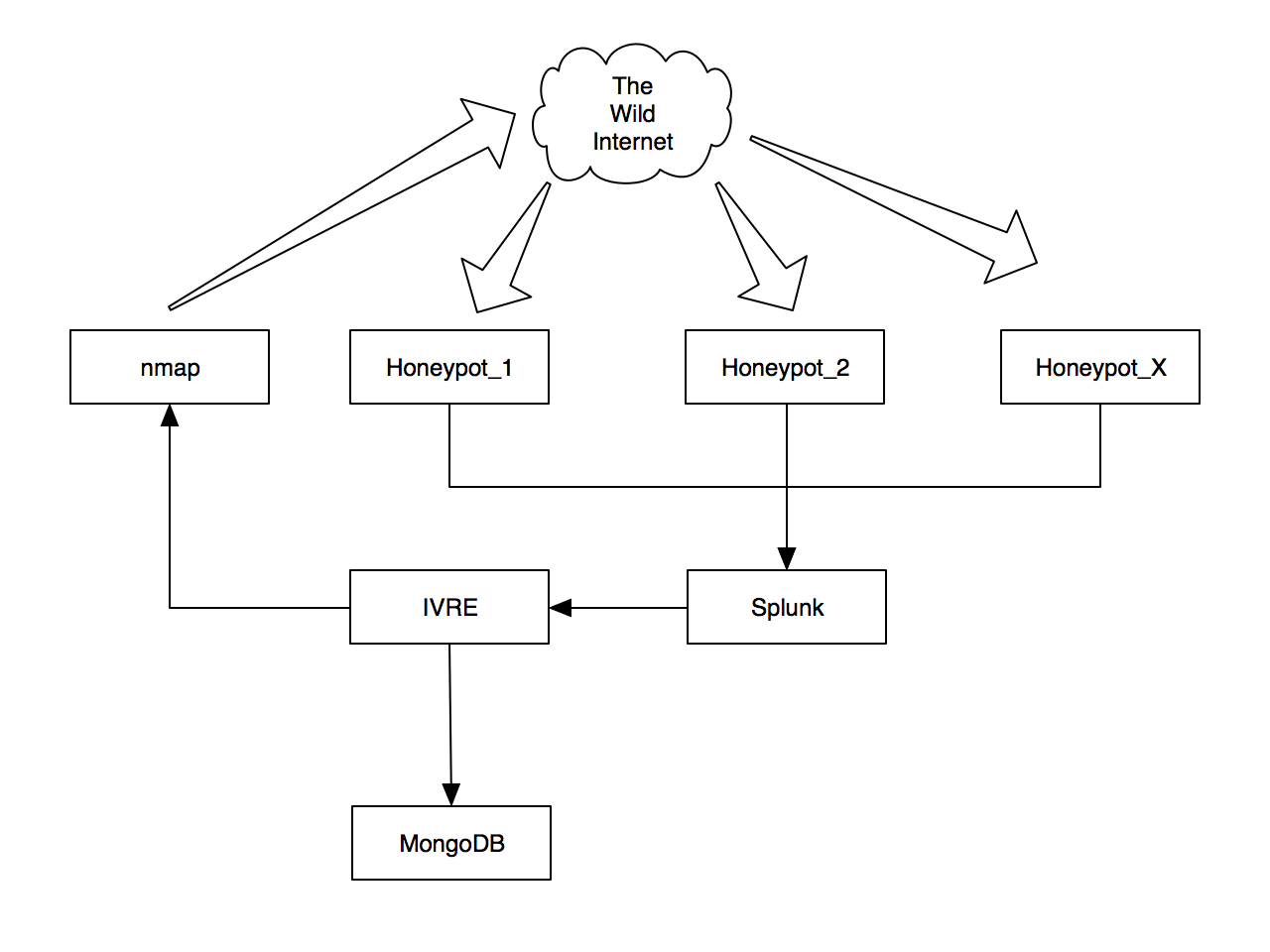
My honeypots data are processed by Splunk which, amongst the generation of dashboards, extract the list of offensive IP addresses and feed IVRE. The IP addresses are scanned using Nmap and the post-processing of results stored in a MongoDB database. The post-processing includes:
- Geo-localization
- Network tagging
- Fingerprinting
- Processing of screenshots
All the results are available through a web interface but also via command line tools. At this time, I already collected info from 3500+ IP addresses:

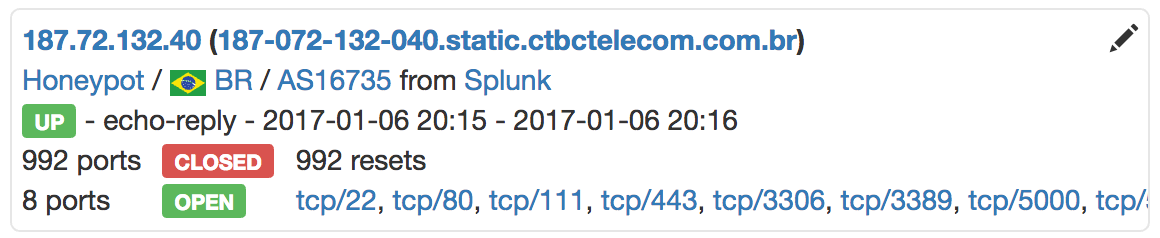
Basic information is display per IP addresses:
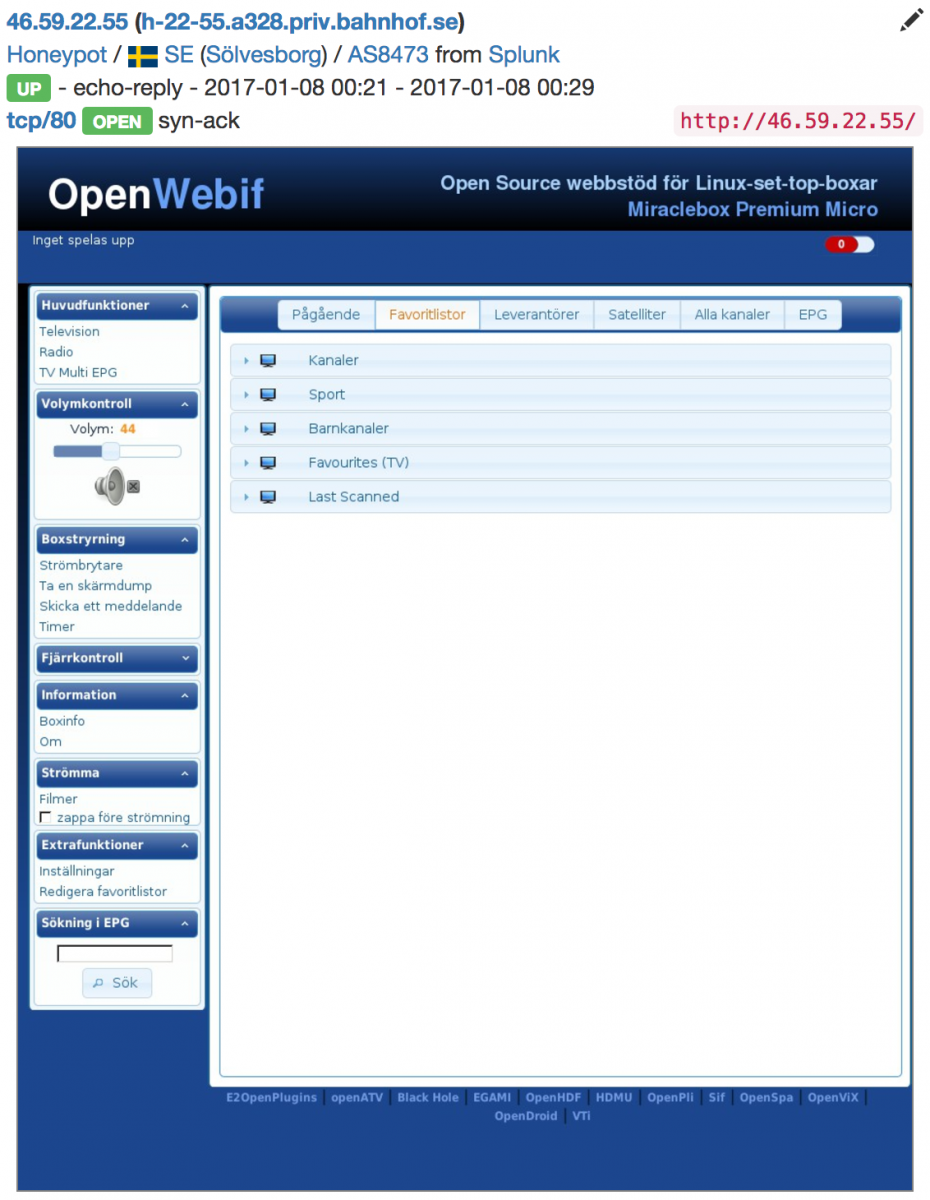
Some reconnaissance features like automatic screenshots:
And sharing of data:
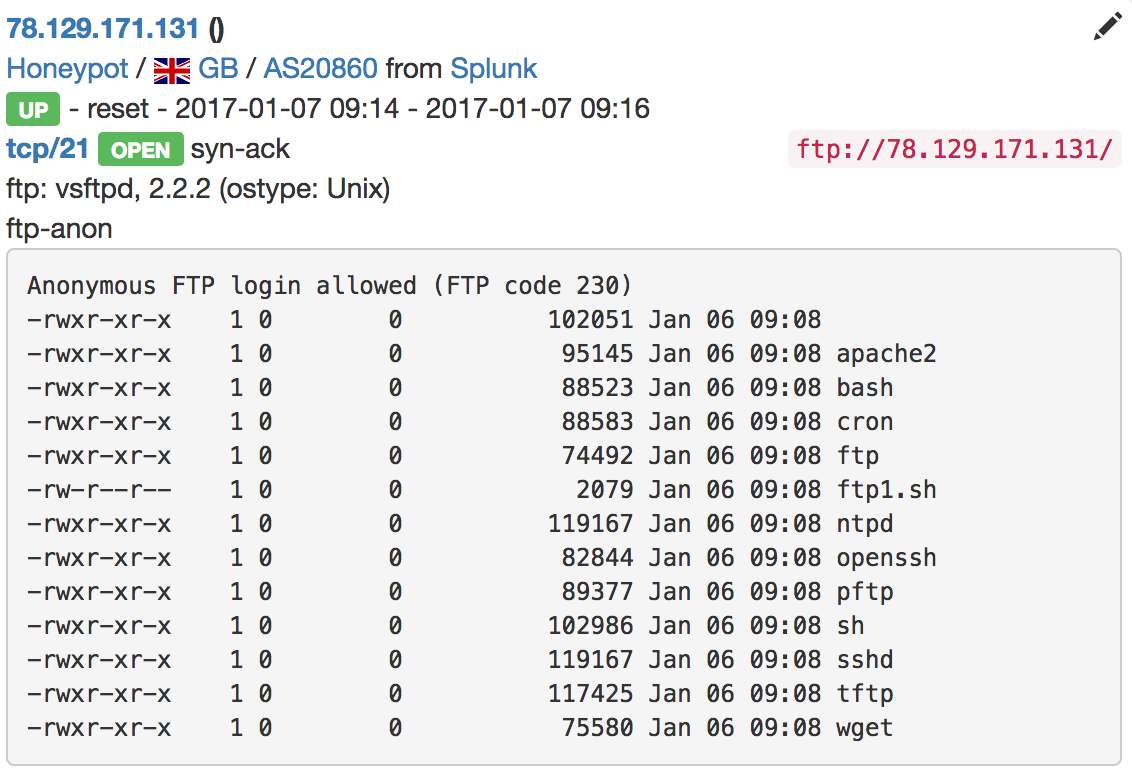
Very useful to find compromized hosts which deliver malware! The web interface provides a powerful search feature. Examples:
- Show me all IP addresses from Russia, that have a port 27017 open (MongoDB)
- Show me the "network devices" from Brazil (switches, routers, firewalls, ...)
- Show me the hosts running MSSQL without password
- Show me the available file shares SMB or NFS (Yes, I found some open NFS servers!)
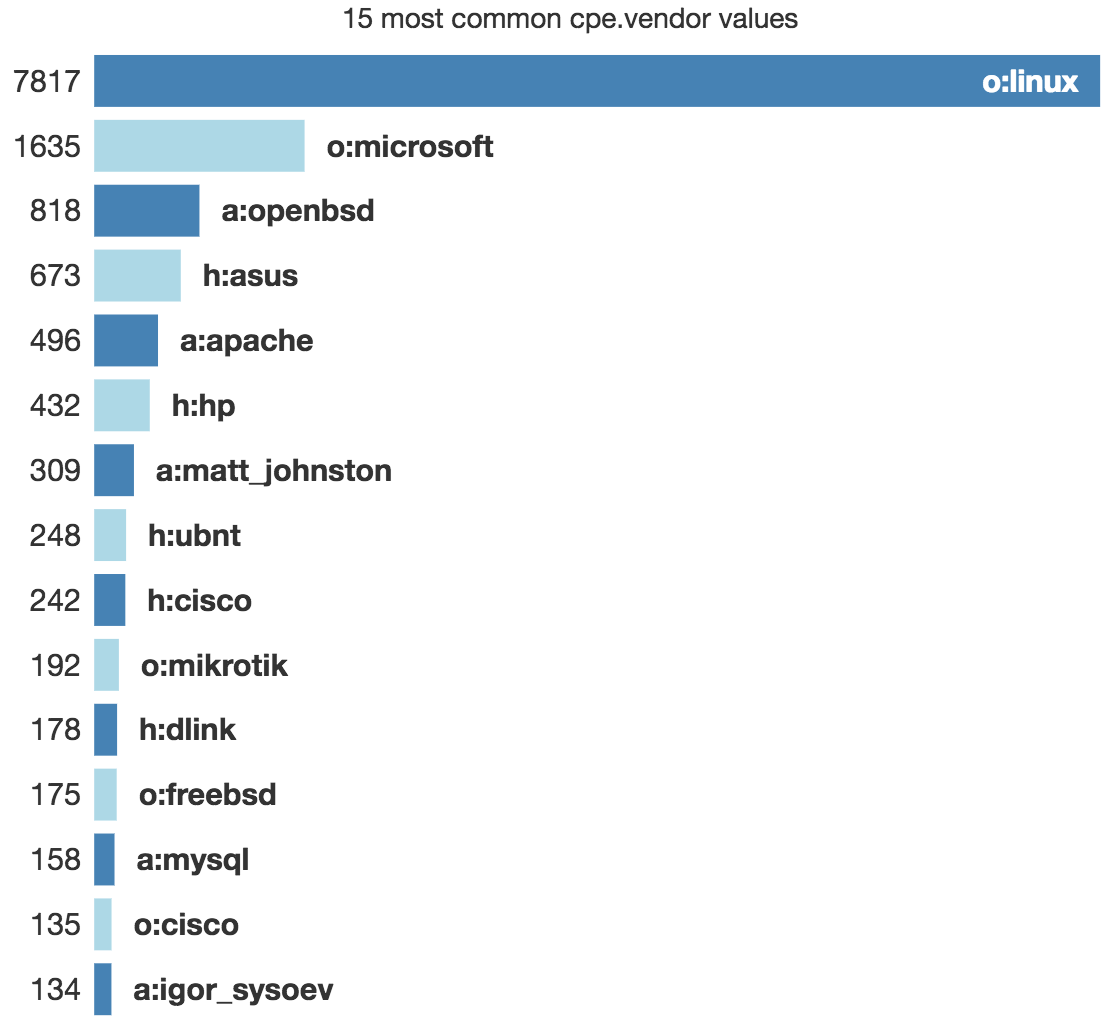
Out of the box, statistics are available. Example, the top CPE detected:
Getting more knowledge about your attackers is always good. IVRE can help you in this way. This is a very powerful framework that will help you to build your own small "Shodan". Happy hunting!
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments