Malicious spam with links to CryptoWall 3.0 - Subject: Domain [name] Suspension Notice
2015-11-05 update: After posting this diary, we started seeing reports of CryptoWall 4.0. One of the people who analyzed this new CryptoWall variant provided me details, which you can read about at: http://malware-traffic-analysis.net/2015/11/05/index.html
Introduction
Since Monday 2015-10-26, we've noticed a particular campaign sending malicious spam (malspam) with links to download CryptoWall 3.0 ransomware. This campaign has been impersonating domain registrars. Conrad Longmore blogged about it last week [1], and Techhelplist.com has a good write-up on the campaign [2]. Several other sources have also discussed this wave of malspam [3, 4, 5, 6, 7, 8 to name a few].
For this diary, we'll take a closer look at the emails and associated CryptoWall 3.0 malware.
The malspam
Based on what I've seen, this malspam was delivered to recipients who didn't use privacy protection when they registered their domains. Their contact information is publicly-listed in the whois records for their domains. Criminals behind the campaign are collecting this publicly-available information, impersonating the registrars, and sending malspam to the email addresses listed as points of contact. Below are two examples of the emails I've found.
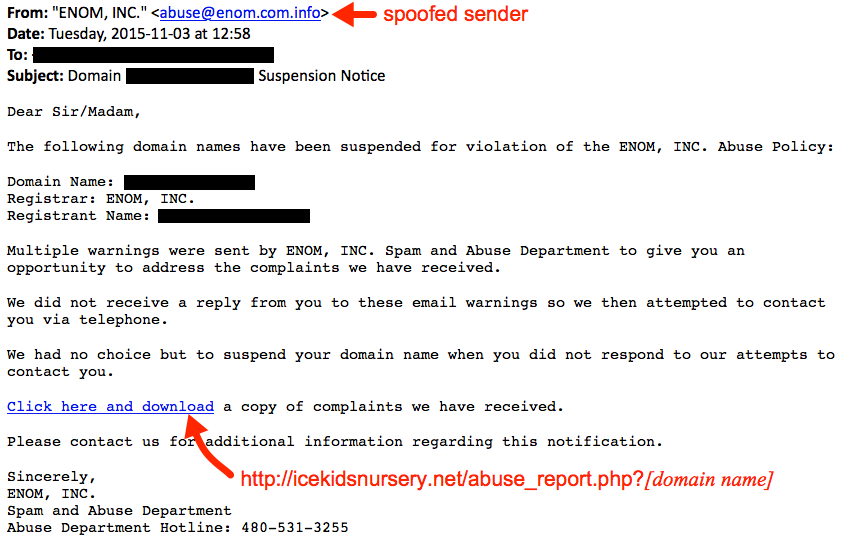
Shown above: Screenshot from one of the emails that spoofed Enom, Inc.
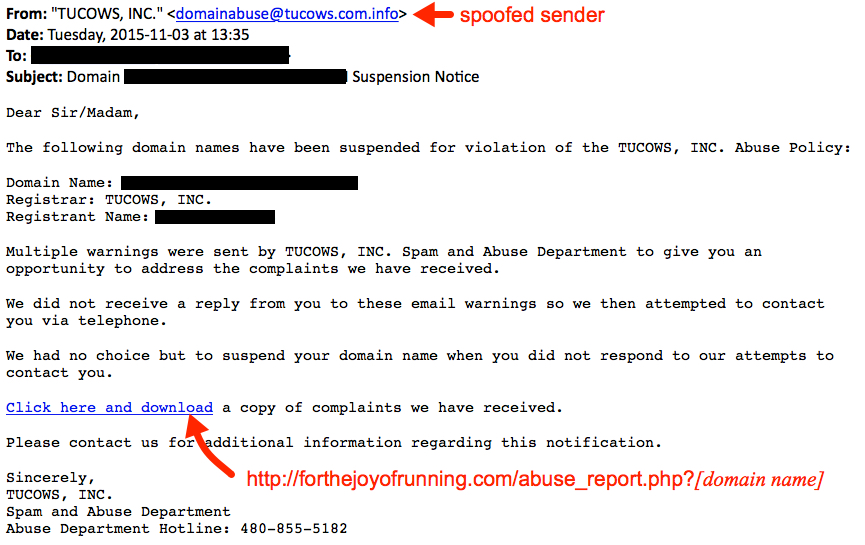
Shown above: Screenshot from one of the emails that spoofed Tucows, Inc.
Enom and Tucows are just two of the many examples people have reported. When looking at the email headers, you'll find these were not sent from the actual registrars. The sender addresses were spoofed.

Shown above: Header lines that show the first example was not sent by Enom, Inc.
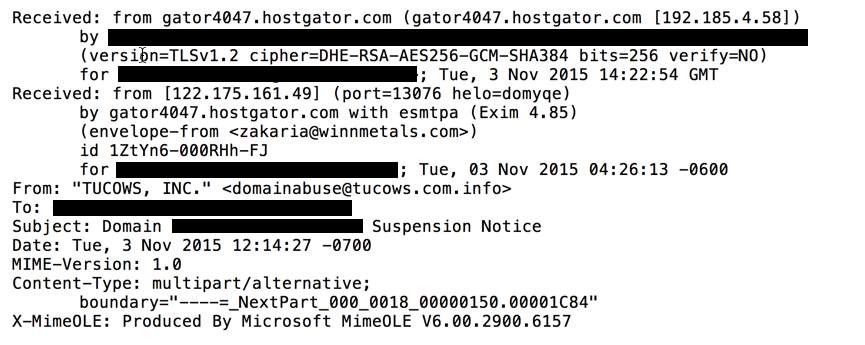
Shown above: Header lines that show the second example was not sent by Tucows, Inc.
If you receive one of the emails, the link follows a specific pattern: http://[unrelated compromised website]/abuse_report.php?[your domain name]. The domain names are not important. You can always get the malware by substituting any string of characters for the domain name in the URL (assuming no one has fixed the compromised website yet).
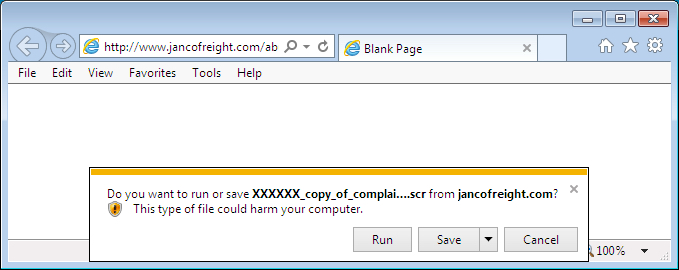
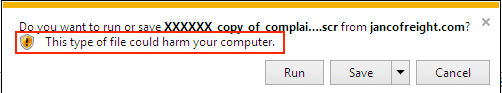
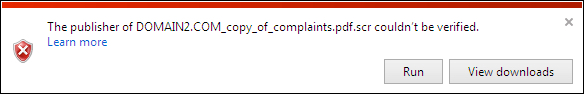
Shown above: I substituted a string of "X"s for the domain name in a URL from one of the emails.
The emails have different senders, and they contain a variety of domains in the URLs to download the malware. I've compiled a list of the first 100 emails I found to provide an idea on the scope of this campaign. Click here for a .CSV file of the list.
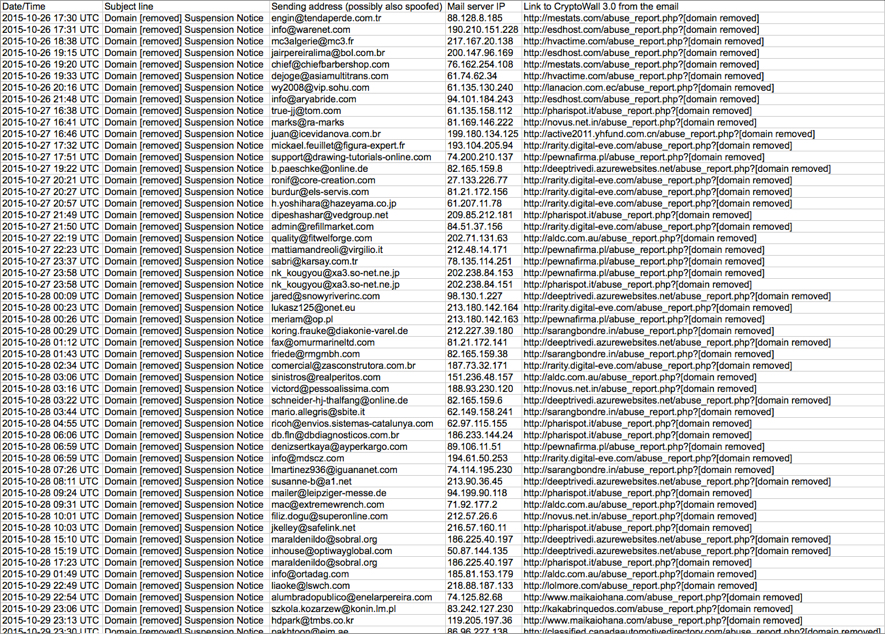
Shown above: Some of the emails seen from this CryptoWall 3.0 malspam campaign.
The malware
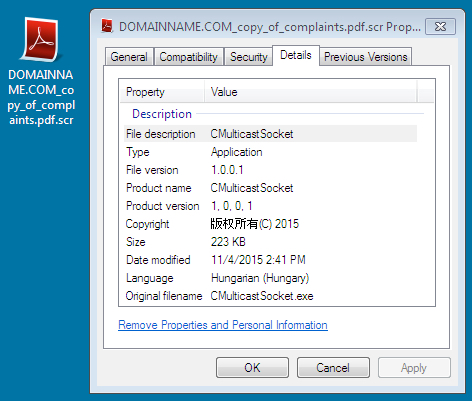
I grabbed a sample of the CryptoWall 3.0 on Tuesday 2015-11-03. The sample was first submitted to Virus Total the previous day (Monday).
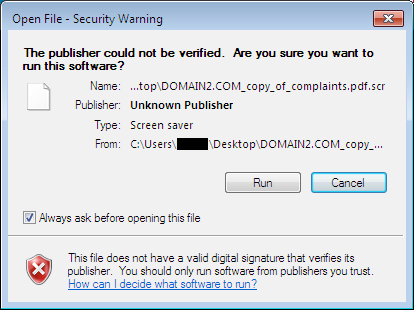
File name: [domain name]_copy_of_complaints.pdf.scr
- File size: 223.0 KB ( 228,354 bytes )
- MD5 hash: 866f551ac050ce293bddfca62110d35a
- SHA1 hash: f11dcc4069e86d09f4b8a5a37a3a56756391ea40
- SHA256 hash: 02f61cebe546041985f4dac3ad6cee83c4cdc6511ec265dc78afcd69c8ac46a9
- First submitted to VirusTotal: 2015-11-02 20:17:03 UTC
- Detection ratio: 25 / 55
- VirusTotal Link - Malwr.com link - Hybrid-Analysis.com link
I ran the sample on two different Windows hosts and got two different Bitcoin addresses for the ransom payment.
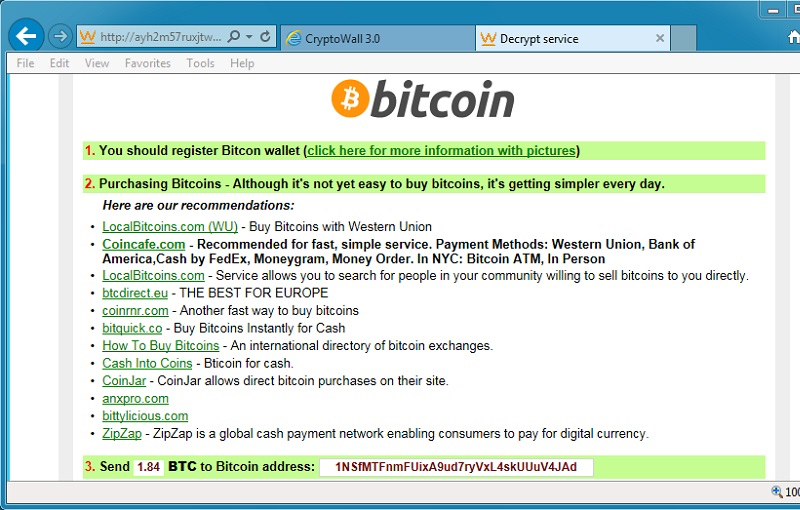
Shown above: Decrypt instructions from the first infection with the CryptoWall 3.0 sample.
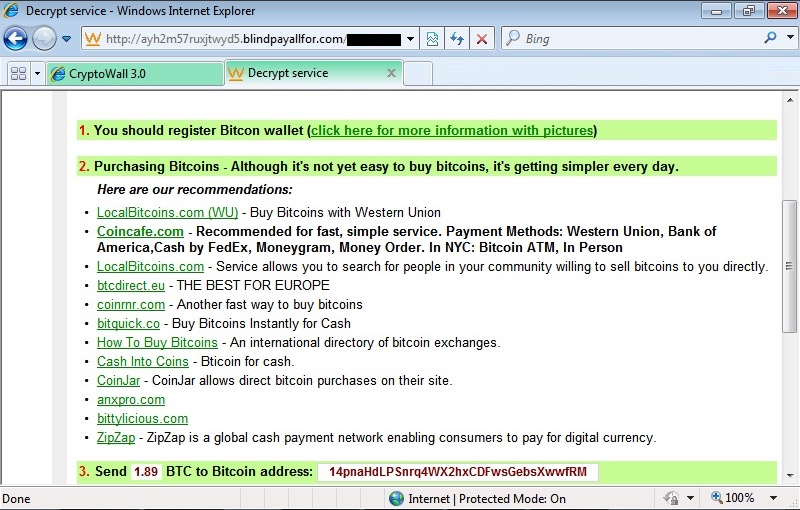
Shown above: Decrypt instructions from the second infection with the same CryptoWall 3.0 sample.
Traffic from the two infected hosts is consistent with CryptoWall 3.0 activity.
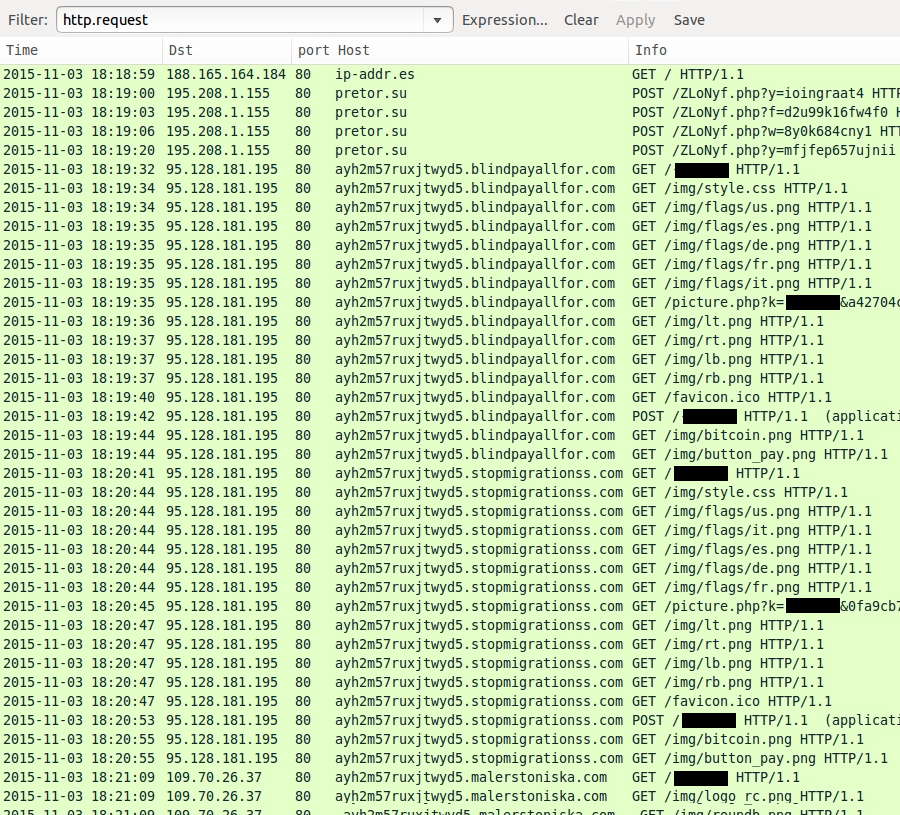
Shown above: Traffic filtered in Wireshark on the first infection with the CryptoWall 3.0 sample.
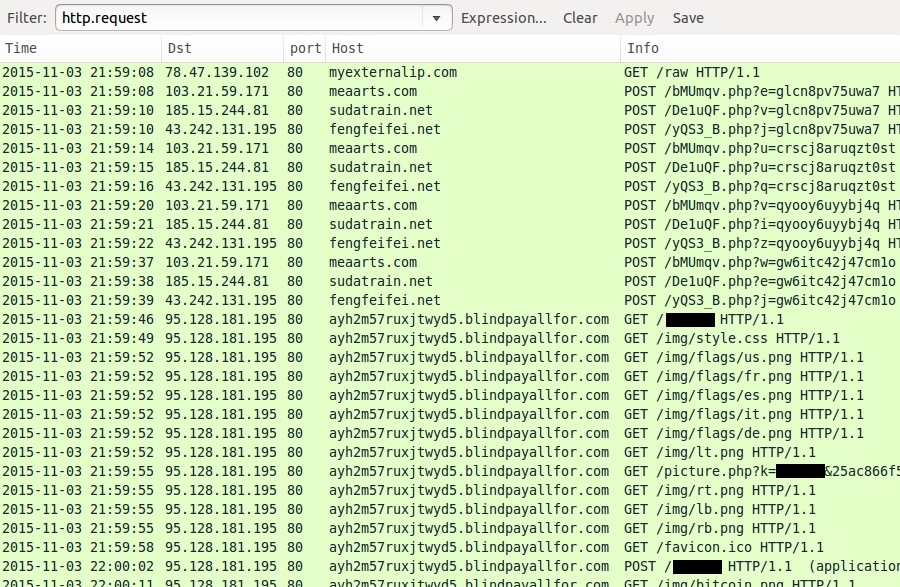
Shown above: Traffic filtered in Wireshark on the second infection with the same CryptoWall 3.0 sample.
I used tcpreplay in Security Onion on a pcap of traffic from the first infection. The EmergingThreats (ET) and ET Pro rulesets showed alerts related to CryptoWall.
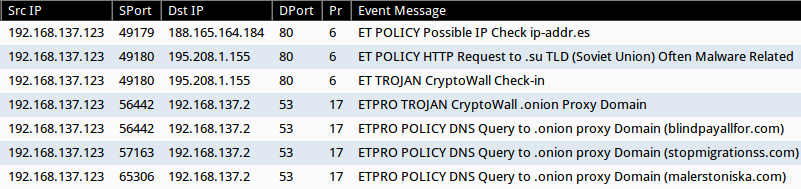
Shown above: ET and ET Pro alerts on traffic from the first infection.
I also used Snort with the Talos Registered ruleset to read the pcap. That showed CryptoWall alerts as well.
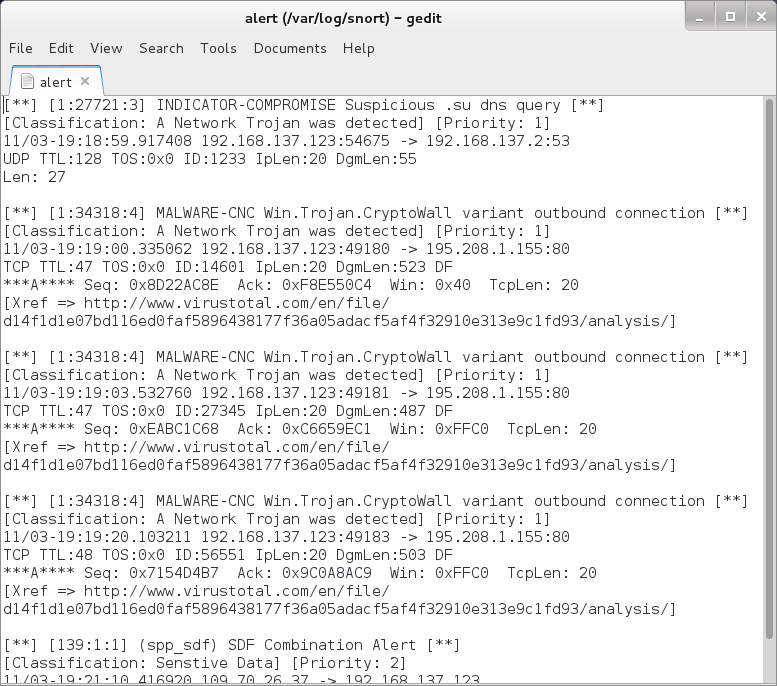
Shown above: Alerts logged after reading a pcap of the infection traffic with Snort.
Final Words
If you receive one of these emails, and you download the file, you should see plenty of warnings the file is not safe. In a company environment, properly-administered Windows hosts should prevent people from running the malware.
In my personal opinion, this malspam isn't a serious threat, especially to anyone aware of computer security. So why do criminals run these campaigns? Apparently, enough of their emails get through, people still fall for the malware, and their Windows computers are configured so they can run it.
As of Wednesday 2015-11-04, I haven't found any more of this malspam. This might be temporary, or the criminals behind it might have started a different campaign. Either way, it's always interesting to see the daily changes in our cyber threat landscape.
Pcaps and the malware sample used in this diary are available here.
---
Brad Duncan
Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
References:
[1] http://blog.dynamoo.com/2015/10/malware-spam-domain-domain-suspension.html
[2] https://techhelplist.com/spam-list/958-domain-suspension-notice-malware
[3] http://botcrawl.com/beware-of-fake-domain-suspension-notice-emails/
[4] https://grahamcluley.com/2015/10/bogus-web-domain-suspension-notice-leads-malware/
[5] http://www.hoax-slayer.com/domain-suspension-notice-malware-emails.shtml
[6] http://domainnamewire.com/2015/10/26/warning-domain-name-phishing-email-blast-going-on-right-now/
[7] http://www.domaininvesting.com/enom-spear-phishing-email-received/
[8] http://www.onlinethreatalerts.com/article/2015/10/29/domain-name-suspension-notice-for-the-violation-of-melbourne-it-ltd-abuse-policy/



Comments