Mandiant Highlighter 2
In previous dairy I discussed the basic usage of Mandiant Highlighter .In this diary I will discuss some other features.
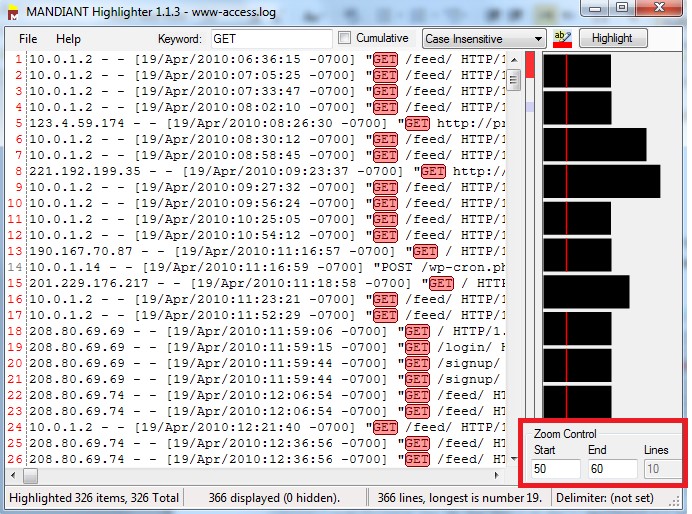
Mandiant Highlighter Graphic
The graphic is an overall view of the whole file. Each line/bar on the graph represents a line in the text, the length are proportional to the line lengths in the file. When you highlight a word on the text it will be highlighted on the graph as well..jpg)
If you would like to specify the range of data that you would like to display, you can do that by entering the range in “Zoom Control” section in the right bottom of the screen:
Windows Event Viewer:
To view Windows events, you have first to export it to .txt file. Here is the steps to Save the event files to text file:
1-Right click on the event category:
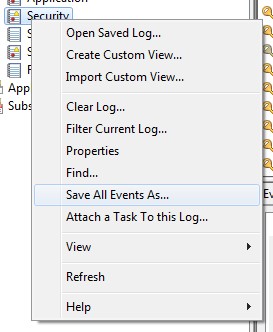
2-Select “Save All Events As ...”
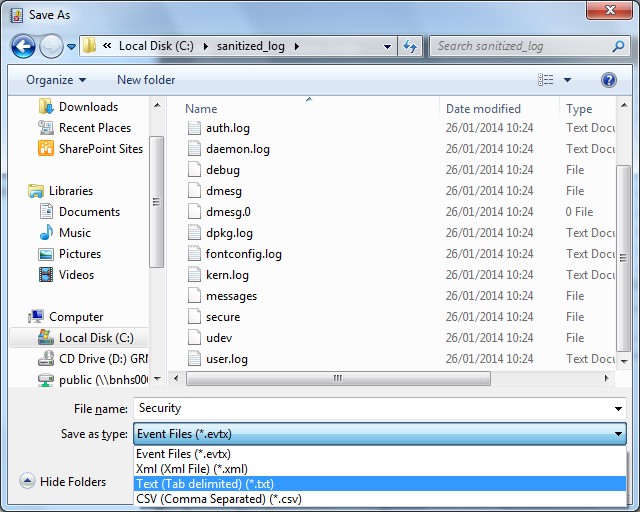
3-Type the file name and select Text from “Save Type As “Drop menu
Now you can use Mandiant Highlighter to parse the Windows Events
Regular Expressions:
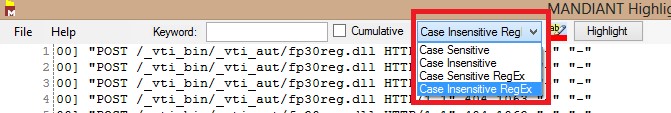
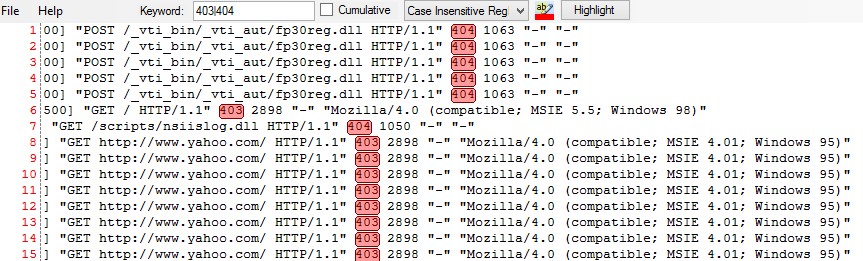
Can you imagine a powerful log parser without regular expression support? To use regular expressions in Mandiant Highlighter enter the regular expression in the Keyword box then select Case Sensitive RegExp/Case Insensitive drop menu


Comments