Fake Epsilon Breach Warning Phishes for Credit Report Customers
Michael Mosbey sent us a link to a website that attempts to scare people into purchasing a credit report. The website, pictured below, reminds the visitor of the relatively recent Epsilon data breach. The goal is to persuade the person into proceeding to another site that is being promoted. This looks like a technique to make money through affiliate marketing.
Fraudulent URL: www. financialalertssystem. com/5/t/14.php?engsec=10&target=example.com (don't go there)
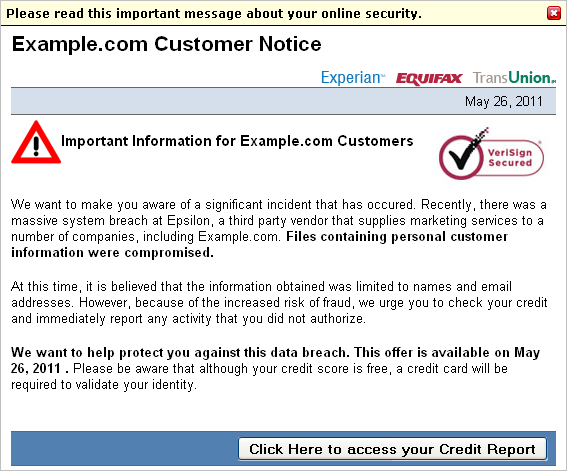
To urge the person to act right away, the website uses a bit of JavaScript to dynamically generate the date during which the offer is available. This allows the website to always present the current date, regardless of when the page is accessed.
The page is written to assist the attacker in targeting multiple domains. It accepts the targeted organization's name as the "target" parameter. For the screenshot above, we used "example.com", so the page stated "Important Information for Example.com Customers."
The page also presents the following (entertaining) disclaimer:
"2011 All right reserved. This site is not sponsored by or affiliated with Example.com. Example.com has not authored, participated in, or in any way reviewed this advertisement or authorized it. Terms and conditions apply, see service providers's site for details. This site is an advertisement. This website, and any page on the website, is based loosely off true stories, and is a fictitious account. Compensation is received for clicks on or purchase of products featured on this site.. For information about the Epsilon system breach, please click here."
-- Lenny Zeltser
Lenny Zeltser leads a security consulting team and teaches how to analyze and combat malware. He is active on Twitter and writes a daily security blog.
MacDefender ups the ante with removing the password need for installation
MacDefender, malware posing as security software that targets Mac OS X, and to which only days ago Apple had responded with instructions and a promise of an OS X update to eradicate the threat, has upped the ante with a new version according to Intego that does not need to ask the user's password any longer.
No, it's not using an exploit to avoid asking the right to write in the /Applications directory, it simply installs the software and activates it for the current user only. Since most macs are using only a single user that changes little for the malware. But it removes the pop-up for your password. Anybody in the admin group can write to the /Applications directory:
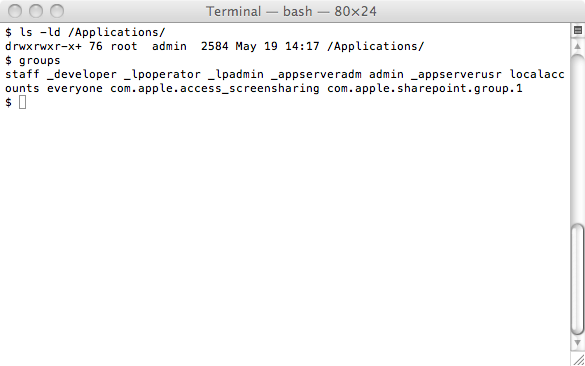
So they do not need to use the graphical sudo functionality as long as you're in the admin group (something administrator accounts are).
Not typing your password when you did not ask for software to be installed was one of those simple rules to explain to the users, guess we're now down to those much harder to explain instructions for our users.
--
Swa Frantzen -- Section 66


Comments