Mozilla Firefox 3.6.12 Remote Denial Of Service
Thanks to our reader Seb for the heads up about a remote denial of service vulnerability within Firefox 3.6.12.
There are a number of sites showing the exploit code which has been developed by Italian members of the BackTrack project.
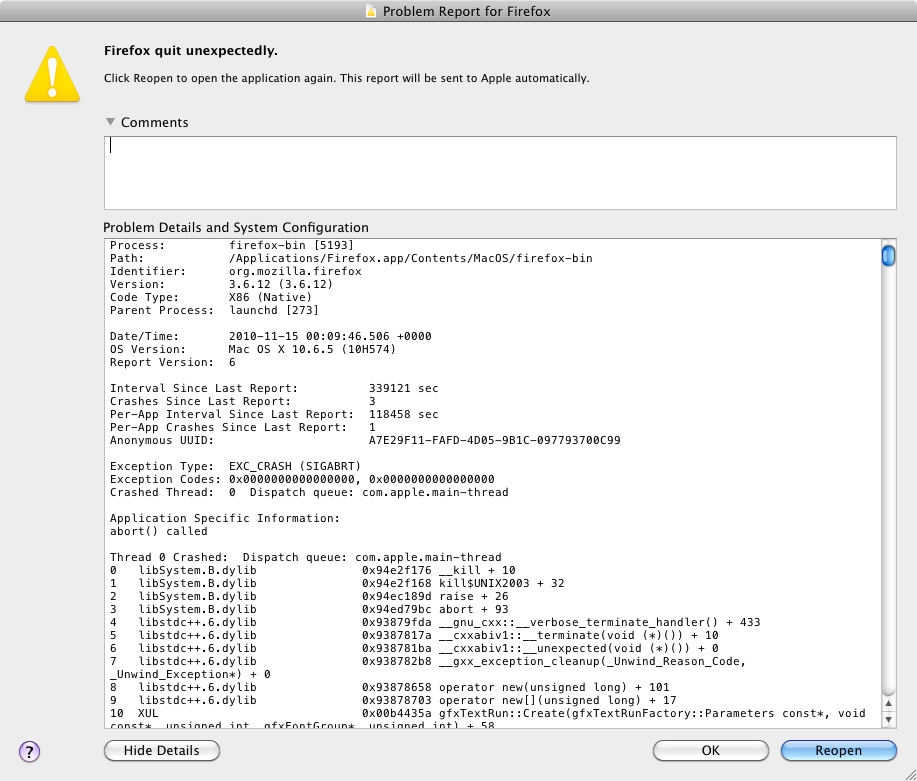
I'll not publish the code here as its easily found with your favourite search engine, but below is a screen shot showing the impact of the code on a fully patched Mac OSX 10.6.5 system.
![]()
![]()
Diary updated after contact with Emanuele Gentili.
Minibis hits beta with Version 2.1
Christian Wojner over at CERT.at has announced that their automated malware analysis environment has been updated.
Version 2.1 is now available in beta form, and he commented that:
"Lots of cool new features, maximum customization, and easy and free to use.
You can even script the sample-execution itself now - that means no more
boundaries regarding sample-types. Scripts for .exe, .dll, .swf, .pdf,
.js as well as for visiting URLs are already on-board."
Futher details over at CERT.at


Comments